Microsoft’s June Patch Tuesday is here, bringing fixes for vulnerabilities impacting its multiple products. This month’s release highlights the ongoing battle against cybersecurity threats, from critical updates to important fixes. Let’s dive into the crucial insights from Microsoft’s Patch Tuesday updates for June 2024.
Microsoft Patch Tuesday’s June 2024 edition addressed 58 vulnerabilities, including one critical and 50 important severity vulnerabilities. In this month’s security updates, Microsoft has addressed one zero-day vulnerability known to be exploited in the wild. Microsoft also addressed seven vulnerabilities in Microsoft Edge (Chromium-based). The vulnerabilities have been patched earlier this month.
Microsoft Patch Tuesday, June edition includes updates for vulnerabilities in Microsoft Office and Components, Visual Studio, Windows Server Service, Windows Kernel, Windows DHCP Server, Azure Storage Library, Azure File Sync, and more.
Microsoft has fixed several flaws in multiple software, including Denial of Service (DoS), Elevation of Privilege (EoP), Information Disclosure, and Remote Code Execution (RCE).
The June 2024 Microsoft vulnerabilities are classified as follows:
| Vulnerability Category | Quantity | Severities |
| Denial of Service Vulnerability | 5 | Important: 5 |
| Elevation of Privilege Vulnerability | 25 | Important: 25 |
| Information Disclosure Vulnerability | 3 | Important: 3 |
| Remote Code Execution Vulnerability | 18 | Critical: 1 Important: 17 |
Zero-day Vulnerabilities Patched in June Patch Tuesday Edition
CVE-2023-50868: MITRE: CVE-2023-50868 NSEC3 closest encloser proof can exhaust CPU
The vulnerability exists in DNSSEC validation that may allow an attacker to exploit standard DNSSEC protocols intended for DNS integrity by using excessive resources on a resolver, causing a denial of service for legitimate users. This vulnerability was disclosed in February and patched in numerous DNS implementations.
Critical Severity Vulnerability Patched in June Patch Tuesday Edition
CVE-2024-30080: Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability
Message Queuing (MSMQ) is a protocol developed by Microsoft to ensure reliable communication between Windows computers across different networks, even when a host is temporarily not connected (by maintaining a message queue of undelivered messages). To exploit this vulnerability, an attacker must send a malicious MSMQ packet to an MSMQ server. On successful exploitation, an attacker may perform remote code execution on the server side.
Other Microsoft Vulnerability Highlights
- CVE-2024-30082 is an elevation of privilege vulnerability in Win32k. An attacker who successfully exploits the vulnerability may gain SYSTEM privileges.
- CVE-2024-35250 is an elevation of privilege vulnerability in the Windows Kernel-Mode Driver. On successful exploitation, an attacker may gain SYSTEM privileges.
- CVE-2024-30084 is an elevation of privilege vulnerability in the Windows Kernel-Mode Driver. To exploit the vulnerability, an attacker must win a race condition. On successful exploitation, an attacker may gain SYSTEM privileges.
- CVE-2024-30085 is an elevation of privilege vulnerability in the Windows Cloud Files Mini Filter Driver. An attacker who successfully exploits the vulnerability may gain SYSTEM privileges.
- CVE-2024-30086 is an elevation of privilege vulnerability in the Windows Win32 Kernel Subsystem. On successful exploitation, an attacker may gain SYSTEM privileges.
- CVE-2024-30087 is an elevation of privilege vulnerability in the Win32k. The attacker would gain the rights of the user running the affected application.
- CVE-2024-30089 is an elevation of privilege vulnerability in the Microsoft Streaming Service. On successful exploitation, an attacker may gain SYSTEM privileges.
- CVE-2024-30091 is an elevation of privilege vulnerability in Win32k. The attacker would gain the rights of the user running the affected application.
- CVE-2024-30088 and CVE-2024-30099 are elevation of privilege vulnerabilities in the Windows Kernel. To exploit them, an attacker must win a race condition. On successful exploitation, an attacker may gain SYSTEM privileges.
Microsoft Release Summary
This month’s release notes cover multiple Microsoft product families and products/versions affected, including, but not limited to, Windows Distributed File System (DFS), Windows Themes, Winlogon, Windows Remote Access Connection Manager, Windows Event Logging Service, Windows Link Layer Topology Discovery Protocol, Windows Container Manager Service, Microsoft WDAC OLE DB provider for SQL, Windows Wi-Fi Driver, Windows Win32K – GRFX, Windows Standards-Based Storage Management Service, Windows Kernel-Mode Drivers, Windows Cloud Files Mini Filter Driver, Windows Win32 Kernel Subsystem, Windows NT OS Kernel, Microsoft Streaming Service, Windows Storage, Windows Routing and Remote Access Service (RRAS), Windows Cryptographic Services, Microsoft Windows Speech, Microsoft Office SharePoint, Microsoft Office, Microsoft Office Word, Microsoft Office Outlook, Dynamics Business Central, Azure Monitor, Azure SDK, Microsoft Dynamics, Windows Perception Service, Azure Data Science Virtual Machines, Microsoft Windows, and Microsoft Edge (Chromium-based).
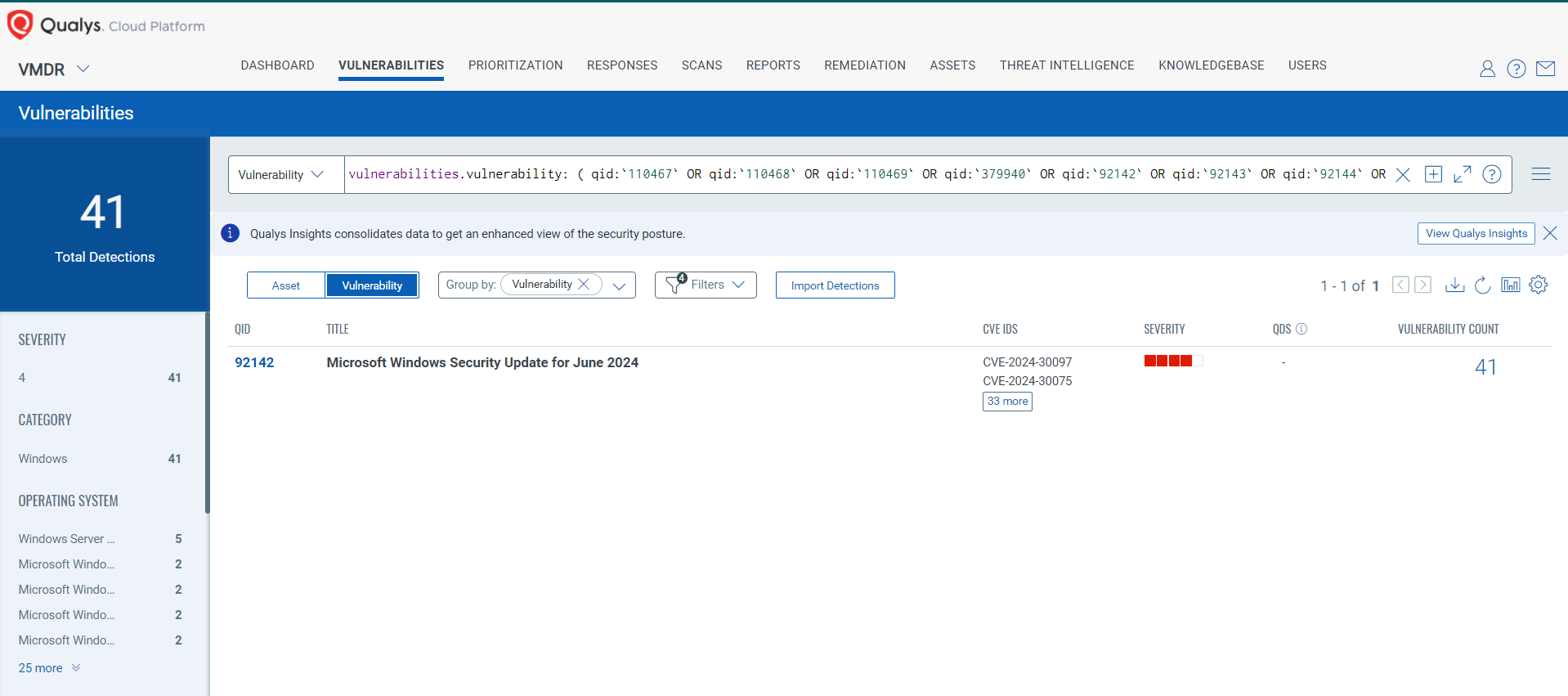
Discover and Prioritize Vulnerabilities in Vulnerability Management, Detection & Response (VMDR)
Qualys VMDR automatically detects new Patch Tuesday vulnerabilities using continuous updates to its Knowledgebase (KB).
You can see all your impacted hosts by these vulnerabilities using the following QQL query:
vulnerabilities.vulnerability: ( qid:`110467` OR qid:`110468` OR qid:`110469` OR qid:`379940` OR qid:`92142` OR qid:`92143` OR qid:`92144` OR qid:`92145` )
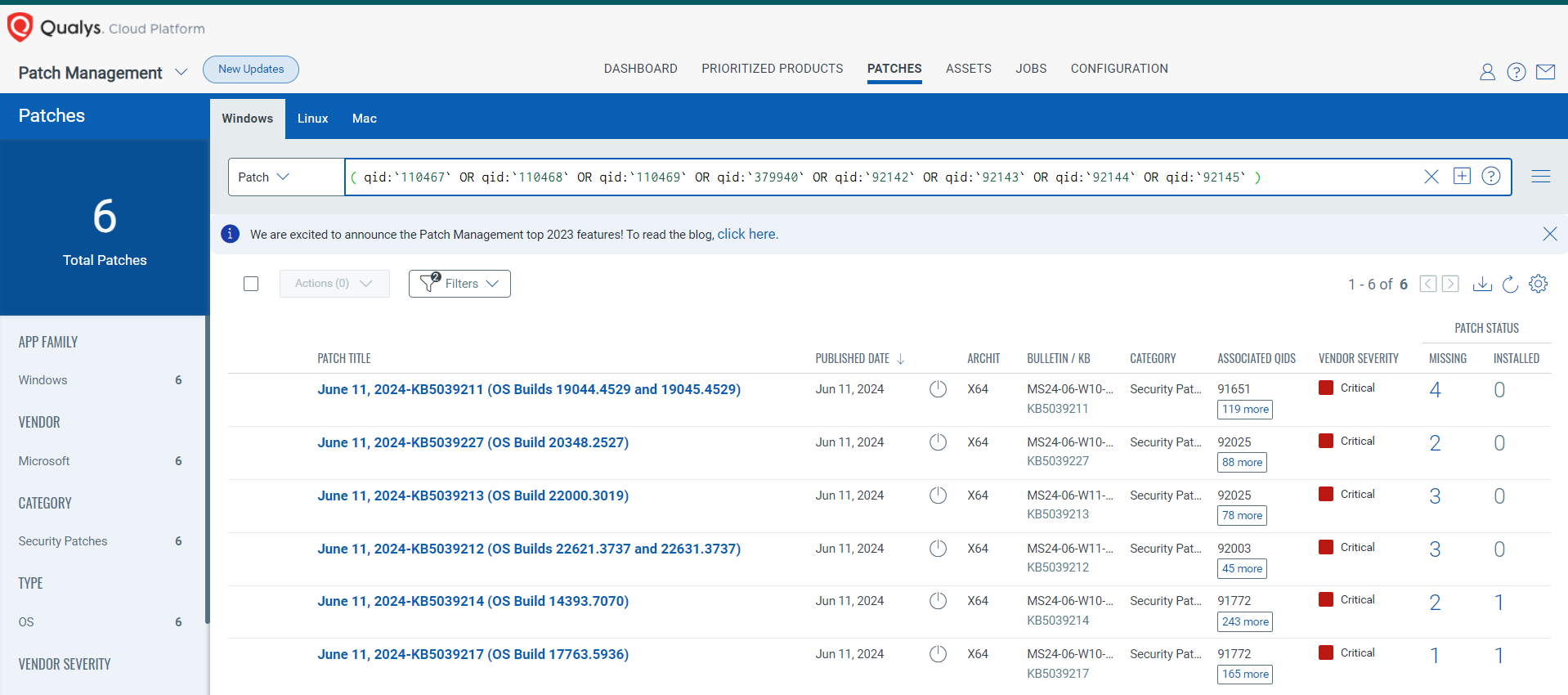
Rapid Response with Patch Management (PM)
VMDR rapidly remediates Windows hosts by deploying the most relevant and applicable per-technology version patches. You can simply select respective QIDs in the Patch Catalog and filter on the “Missing” patches to identify and deploy the applicable, available patches with one click.
The following QQL will return the missing patches for this Patch Tuesday:
( qid:`110467` OR qid:`110468` OR qid:`110469` OR qid:`379940` OR qid:`92142` OR qid:`92143` OR qid:`92144` OR qid:`92145`)
EVALUATE Vendor-Suggested Mitigation with Policy Compliance (PC)
With Qualys Policy Compliance’s Out-of-the-Box Mitigation or Compensatory Controls, the risk of a vulnerability being exploited is reduced when the remediation (fix/patch) cannot be implemented immediately.
Qualys Policy Compliance team releases these exclusive controls based on vendor-suggested Mitigation/Workaround.
Mitigation refers to a setting, standard configuration, or general best-practice existing in a default state that could reduce the severity of the exploitation of a vulnerability.
A workaround is sometimes used temporarily to achieve a task or goal when the usual or planned method isn’t working. Information technology often uses a workaround to overcome hardware, programming, or communication problems. Once a problem is fixed, a workaround is usually abandoned.
The following Qualys Policy Compliance Control IDs (CIDs), and System Defined Controls (SDC) have been updated to support Microsoft recommended mitigation(s) for this Patch Tuesday:
CVE-2024-30080: Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability
CVSS:3.1 9.8 / 8.5 Policy Compliance Control IDs (CIDs):
- 14297 Status of the open network connections and listening ports (Qualys Agent only)
- 14916 Status of Windows Services
- 4030 Status of the Windows Message Queuing Service
The following QQL will return a posture assessment for the CIDs for this Patch Tuesday: control.id: [14297, 14916, 4030] 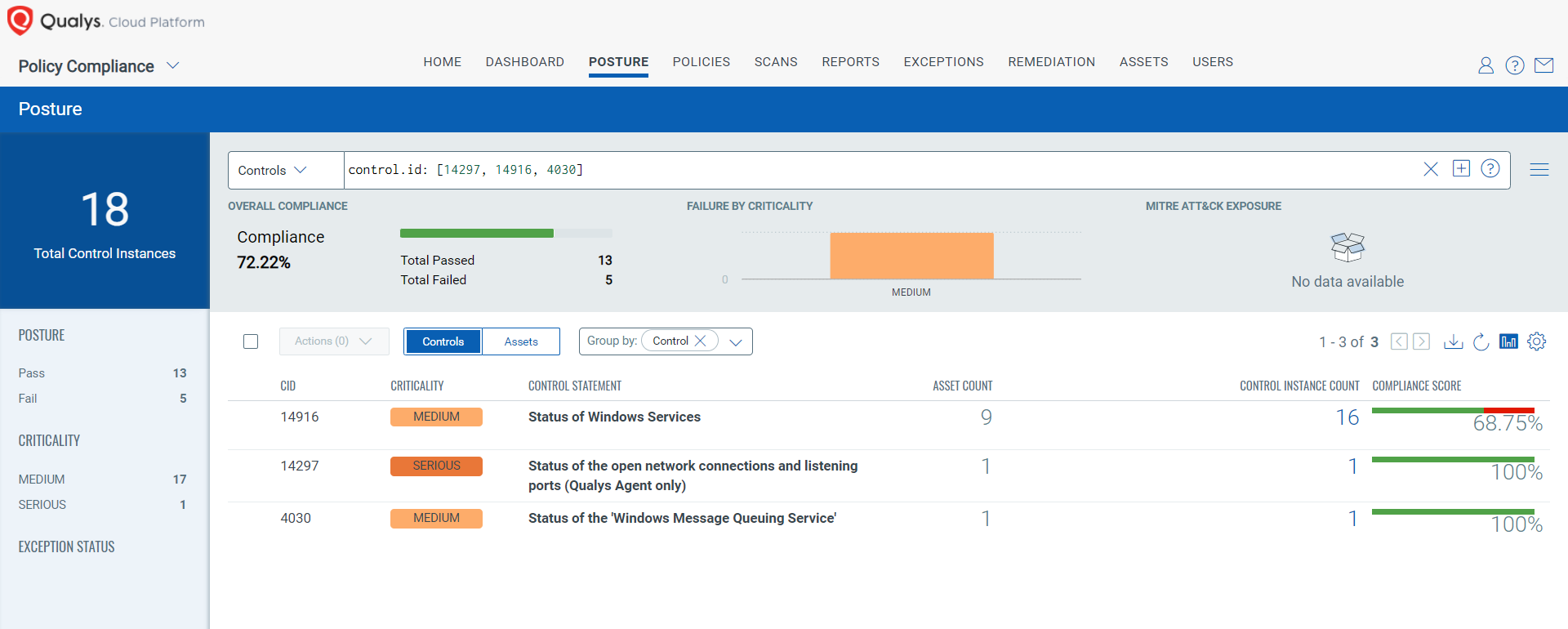
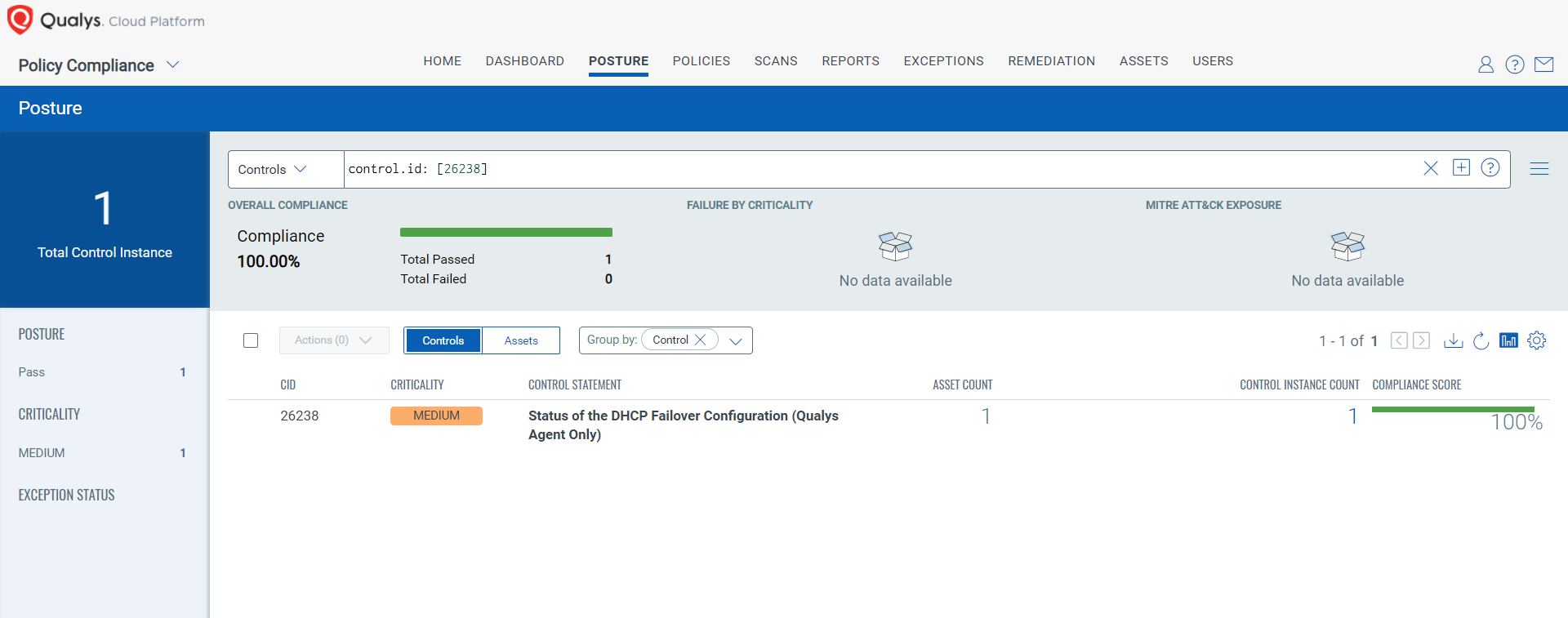
CVE-2024-30070: DHCP Server Service Denial of Service Vulnerability
CVSS:3.1 7.5 / 6.7 Policy Compliance Control IDs (CIDs):
- 26238 Status of the DHCP Failover Configuration (Qualys Agent Only)
The following QQL will return a posture assessment for the CIDs for this Patch Tuesday: control.id: [26238]
Visit the June 2024 Security Updates page to access the full description of each vulnerability and the systems it affects.
Qualys customers can scan their network with QIDs 110467, 110468, 110469, 379940, 92142, 92143, 92144, and 92145 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References:
https://msrc.microsoft.com/update-guide/
https://msrc.microsoft.com/update-guide/releaseNote/2024-Jun
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-30080
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-50868