Summary:
In the first week of March 2020, an old remote code execution vulnerability affecting the PPP daemon (pppd) software that comes installed on almost all Linux based operating systems, as well as powers the firmware of many other networking devices. CVE-2020-8597 have CVSS Score of 9.8 can be remotely exploited by unauthenticated attackers.
Description:
PPP is the protocol used for establishing internet links over dial-up modems, DSL connections, and many other types of point-to-point links including Virtual Private Networks (VPN) such as Point to Point Tunneling Protocol (PPTP). The pppd software can also authenticate a network connected peer and/or supply authentication information to the peer using multiple authentication protocols including EAP.
“This vulnerability is due to an error in validating the size of the input before copying the supplied data into memory. As the validation of the data size is incorrect, arbitrary data can be copied into memory and cause memory corruption, possibly leading to the execution of unwanted code,” the advisory says. “The vulnerability is in the logic of the eap parsing code, specifically in the eap_request() and eap_response() functions in eap.c that are called by a network input handler.”
The affected pppd software is an implementation of Point-to-Point Protocol (PPP) that enables communication and data transfer between nodes, primarily used to establish internet links such as those over dial-up modems, DSL broadband connections, and VPNs.
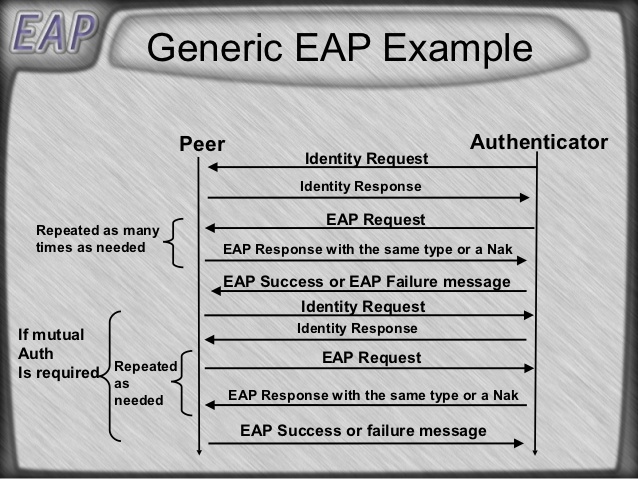
Image Source: https://www.slideshare.net/adityammehta/eap-edit
The pppd often runs with high privileges (system or root) and works in conjunction with kernel drivers. This makes it possible for an attacker to potentially execute arbitrary code with system or root level privileges.
There is at present no evidence the vulnerability is being exploited in the wild.
At Qualys Labs, we’ve tried to resolve the issue, reported for CVE-2020-8597.
Affected Products:
Point-to-Point Protocol Daemon versions 2.4.2 through 2.4.8.
OS
- Debian
- Ubuntu
- SUSE Linux
- Fedora
- NetBSD
- Red Hat Enterprise Linux
Applications
- Cisco CallManager
- TP-LINK products
- OpenWRT Embedded OS
- Synology (DiskStation Manager, VisualStation, Router Manager)
Advisory:
https://lists.opensuse.org/opensuse-security-announce/2020-03/msg00006.html
https://quickview.cloudapps.cisco.com/quickview/bug/CSCvs95534/
https://access.redhat.com/errata/RHSA-2020:0630
https://access.redhat.com/errata/RHSA-2020:0631
https://access.redhat.com/errata/RHSA-2020:0633
https://access.redhat.com/errata/RHSA-2020:0634
https://www.tp-link.com/en/support/faq/2803/
https://lists.debian.org/debian-lts-announce/2020/02/msg00005.html
https://usn.ubuntu.com/4288-1/
https://www.debian.org/security/2020/dsa-4632
Mitigation:
Users with affected operating systems and devices are advised to apply security patches as soon as possible, or when it becomes available.
Qualys customers can scan their network with QID(s)# 238006, 238005, 238003, 173081, 197804 to detect vulnerable assets. Kindly continue to follow on Qualys Threat Protection for more coverage on vulnerabilities.
Reference & Sources:
- https://en.wikipedia.org/wiki/Extensible_Authentication_Protocol
- https://github.com/paulusmack/ppp
- https://w1.fi/wpa_supplicant/devel/eap_8c.html