Summary:
Oracle WebLogic Server is a Java EE application server currently developed by Oracle Corporation. In the Oracle Critical Patch Update Advisory – January 2020, Oracle officially fixed a high-risk vulnerability (CVE-2020-2555) that affect to Oracle Coherence library in Oracle WebLogic Server.
Description:
Easily exploitable vulnerability allows unauthenticated attacker with network access via T3 protocol to compromise Oracle Coherence. Successful attacks of this vulnerability can result in takeover of Oracle Coherence.
This critical vulnerability affects the Oracle Coherence library, which is used in popular products such as Oracle WebLogic Server. The root cause of the vulnerability exists in a Java method, which can be called by an attacker and can control related parameters. In Java, when re-creating the object graph, class readObject(), or readExternal() will be called automatically. Therefore, these two methods (and other methods reachable inside the method) can be considered as the root point of deserializing the gadget. The patch toString() removes extract() all calls to the extract() method, and the importance of the method will be analyzed in the following . This modification operation particularly interesting because toString() can be reached via the readObject() method of various standard JRE classes such as BadAttributeValueExpException:
In computing, a sink, event sink or data sink is a class or function designed to receive incoming events from another object or function. Sinks are Java method calls known to have hazardous side effects. Examples of such side effects are:
- Arbitrary file creation via a call to FileOutputStream.write().
- Arbitrary command execution via a call to Runtime.exec().
- Arbitrary method invocation via a call to Method.invoke().
Similarly, the Coherencelibrary also provides such a class ChainedExtractor, that allows to concatenate extract() calls:
The call chain is as follows:
BadAttributeValueException.readObject -> TiedMapEntry.toString -> LazyMap.get -> ChainedTransformer.transform
The Coherence library in which one is able to deliver a malicious serialized object can hence be exploited for remote code execution.
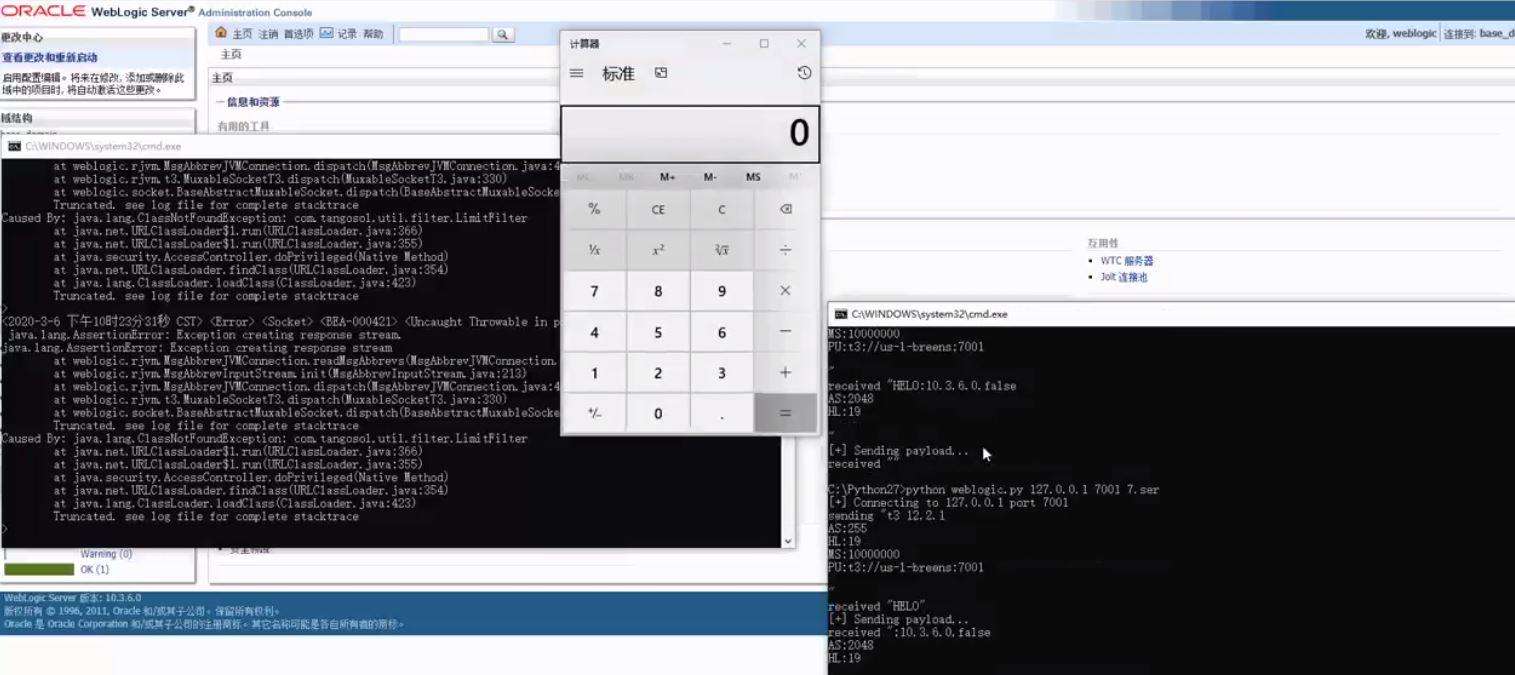
Image Source: https://twitter.com/i/status/1235937745177989121
Affected Products:
Oracle Coherence 3.7.1.17
Oracle Coherence 12.1.3.0.0
Oracle Coherence 12.2.1.3.0
Oracle Coherence 12.2.1.4.0
Advisory:
https://www.oracle.com/security-alerts/cpujan2020.html
Mitigation:
Oracle releases the patch to fix this vulnerability. Users should upgrade Oracle Coherence as soon as possible. It is recommended that users using Weblogic turn off or disable the T3 protocol to avoid malicious attacks.
Enter the WebLogic console, in the base_domain configuration page, go to the Security tab page, click Filter, and configure the filter. Enter in the connection filter: weblogic.security.net.ConnectionFilterImpl, enter 7001 deny t3 t3s in the connection filter rule box to save the effect (requires restart).
Qualys customers can scan their network with QID(s)# 372345 to detect vulnerable assets. Kindly continue to follow on Qualys Threat Protection for more coverage on vulnerabilities.
References & Sources:
- https://meterpreter.org/cve-2020-2555-oracles-weblogic-server-remote-code-execution-vulnerability-alert/
- https://www.youtube.com/watch?v=VzmZTYbm4Zw
- https://www.thezdi.com/blog/2020/3/5/cve-2020-2555-rce-through-a-deserialization-bug-in-oracles-weblogic-server
- https://packetstormsecurity.com/files/157054/Oracle-Coherence-Fusion-Middleware-Remote-Code-Execution.html
- https://twitter.com/i/status/1235937745177989121