Overview
A Privilege Escalation vulnerability has found in the Symantec Endpoint Protection (SEP) which allows attacker to create file anywhere in the system.
Description
Symantec Endpoint Protection create scanning log at “C:\Users\%username%\AppData\Local\Symantec\Symantec Endpoint Protection\Logs” with high privileges
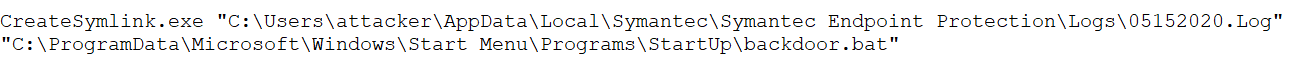
It’s possible to save scanning logs at different location using symbolic link. In windows to create symbolic link use CreateSymLink tool.
For storing log file content in startup folder, following command is used,
Using symbolic link, we can write log files in other file formats which can lead to an Elevation of Privilege.
Exploitation:
To run exploit available on Github, provide two arguments. First argument is file path where you want to write log
![]()
Second argument is name of the file,
![]()
We have two arguments, now run the exploit using below command
![]()
SEP tool – DoScan will scanned the files and saved logs in backdoor.bat file. Filename which is PowerShell command contains base64 encoded data, after decoding got following command,
![]()
A low privilege user can copy any file under the C:\Users\Public\ folder, for testing copy calc.exe application and rename it to 1.exe.
When administrator login to the system, backdoor.bat file is executed and calculator pops ups.
Affected Products
SEP 14.2 RU2
Advisory
To protect your system from attack, patch with recent update from Symantec web page
Mitigation
Take following measure to reduce risk of attack,
- Restrict remote access to trusted systems only.
- Run under the least privilege, where possible, to limit the impact of potential exploit.
- Keep updated all operating systems and applications.
References & Sources:
https://github.com/RedyOpsResearchLabs/SEP-14.2-Arbitrary-Write