The second and effective zero day on Chromium-based browsers such as Google Chrome and Microsoft Edge was posted consecutively, just after yesterday’s zero-day RCE. This time, Frust, a security researcher, tweeted about a zero-day remote code execution vulnerability creating havoc in the browser-based vulnerability trend. He has released a working proof-of-concept exploit.
Unless a threat actor chains the new zero-day with an unpatched sandbox escape vulnerability, the new zero-day in its current state cannot harm users unless they disable the sandbox. Browser’s sandbox is a security protection that prevents malicious code from reaching the underlying OS.
Once the sandbox is disabled, the PoC exploits browsers to launch the notepad app on Windows 10 devices. At Qualys labs, we’ve tried to recreate the lab environment and successfully tested the PoC on latest deployment of Chrome (90.0.4430.72) as well as Microsoft Edge (89.0.774.77) browsers.
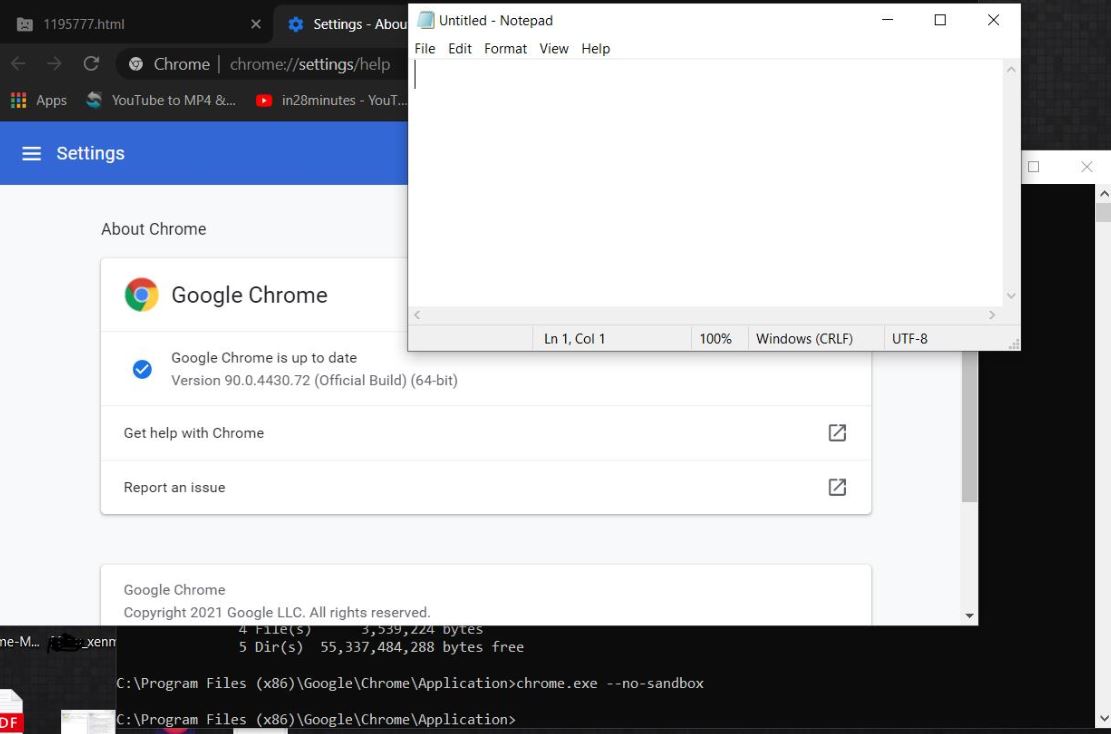
Image Source: Qualys
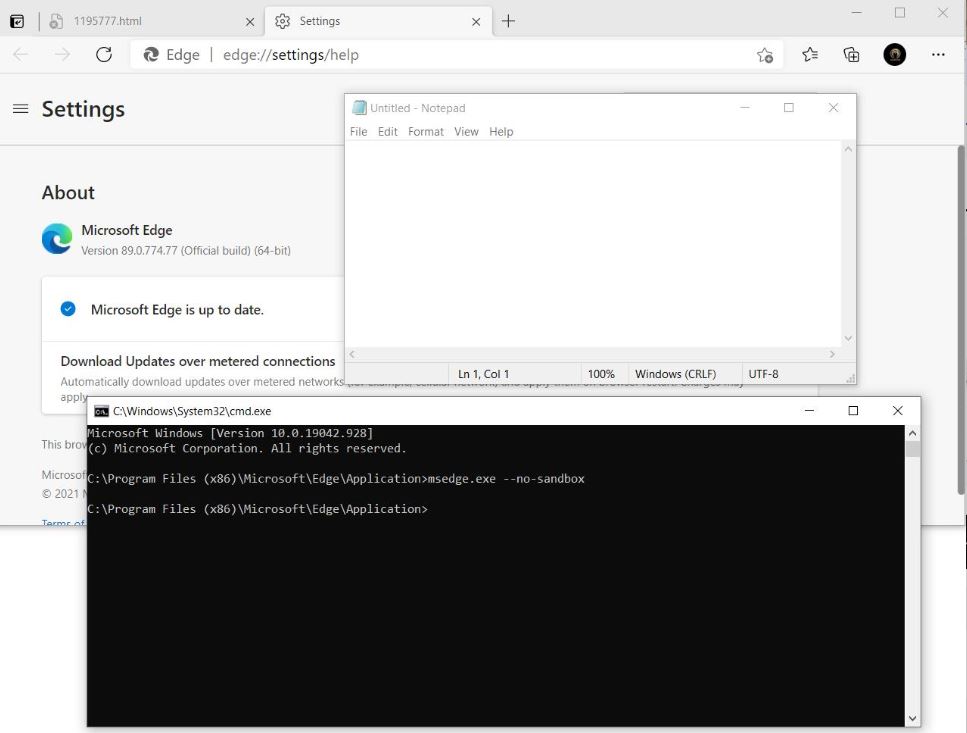
Image Source: Qualys
According to latest updates, patches for this new exploit are being worked on and will be available soon as said by the browser giants.
Affected products
- Google Chrome prior to 90.0.4430.72
- Microsoft Edge prior to 89.0.774.77
Qualys Detection
Qualys customers can scan their network with QID(S) 375461 and 375463 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage on latest vulnerabilities.
References and Sources
https://chromereleases.googleblog.com/2021/04/stable-channel-update-for-desktop_14.html
https://www.youtube.com/embed/qZFzuHNqazo
https://github.com/avboy1337/1195777-chrome0day
https://twitter.com/frust93717815/status/1382307630769598466
https://twitter.com/PatrizioBytes/status/1382416482684964870