Webmin is a web-based system administration tool for Unix-like servers, and services with over 1,000,000 installations worldwide. Using Webmin, you can configure operating system internals, such as users, disk quotas, services, or configuration files, as well as modify, and control open-source apps, such as BIND DNS Server, Apache HTTP Server, PHP, MySQL, and many more.
In May 2021, two security researchers namely Meshal and Mohammed collaborated to discover Remote Code Execution (RCE) vulnerabilities through XSS as well as CSRF in Webmin’s running process feature. These vulnerabilities translated into three CVEs (CVE-2021-31760, CVE-2021-31761, CVE-2021-31762). These flaws were critical and classified under CWE-352 and CWE-79. The PoC used to exploit these vulnerabilities utilized bad implementation referrer header as well as running process endpoint to complete the salvation.
If Webmin is installed using the non-recommended setup.pl script, checking for unknown referrers is not enabled by default. This opens the system up to XSS and CSRF attacks using malicious links. Fortunately the standard RPM, Deb, TAR and Solaris packages do not use this script and so are not vulnerable.
CVE-2021-31760
Cross Site Request Forgery (CSRF) to achieve Remote Command Execution (RCE) through Webmin’s running process feature.
CVE-2021-31761
Reflected Cross Site Scripting (XSS) to achieve Remote Command Execution through Webmin’s running process feature.
CVE-2021-31762
Cross Site Request Forgery (CSRF) to create a privileged user through Webmin’s add users feature, and then get a reverse shell through Webmin’s running process feature.
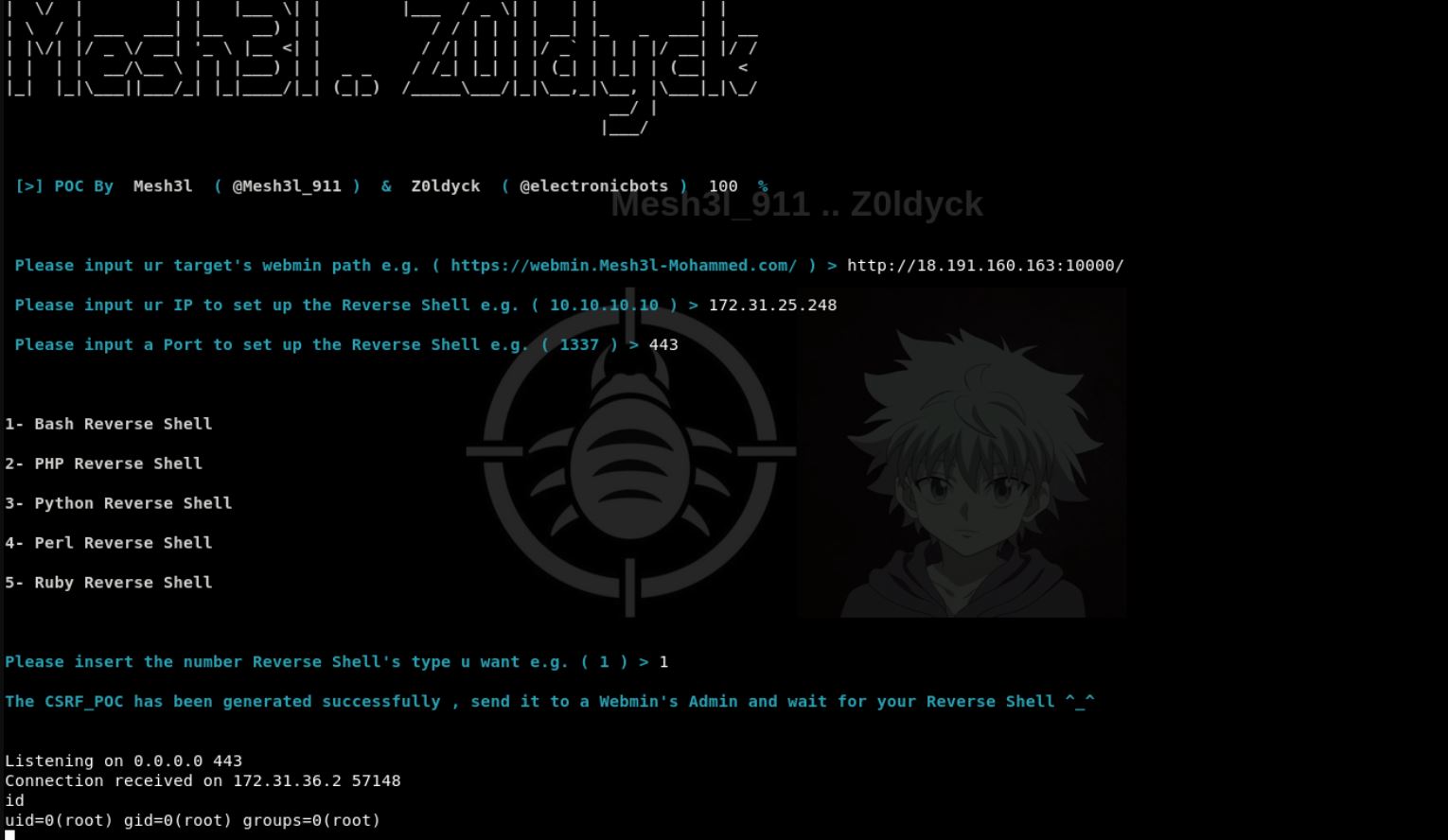
Image Source: Github
Affected products
Webmin version 1.973 or lower
Mitigation
Update Webmin to version 1.974 or add
referers_none = 1
to / etc / webmin / config
Qualys Detection
Qualys customers can scan their network with QID(s) 730087 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage on latest vulnerabilities.
References and Sources
http://www.webmin.com/security.html
https://github.com/electronicbots/CVE-2021-31760
https://github.com/Mesh3l911/CVE-2021-31760
https://github.com/webmin/webmin
https://github.com/Mesh3l911/CVE-2021-31760
https://nvd.nist.gov/vuln/detail/CVE-2021-31760