Google has released the latest Chrome version to address a zero-day vulnerability (CVE-2022-3075). Google has rated this vulnerability as high severity and acknowledged that it has been actively exploited in the wild.
This high severity vulnerability exists due to insufficient data validation in Mojo, which is a group of runtime libraries that offer a platform-independent method of inter-process communication (IPC).
CVE-2022-3075 is the sixth zero-day vulnerability that was detected in Chrome since the start of the year. Following are the previous zero-days in chronological order:
- CVE-2022-2856: Insufficient validation of untrusted input in Intents (August 17th)
- CVE-2022-2294: Heap-based buffer overflow vulnerability in the WebRTC (Web Real-Time Communications) component (July 4th)
- CVE-2022-1364: Type confusion in V8 (April 14th)
- CVE-2022-1096: Type confusion flaw in the Chrome V8 JavaScript engine (March 25th)
- CVE-2022-0609: Use-after-free in Animation (February 14th)
Affected versions
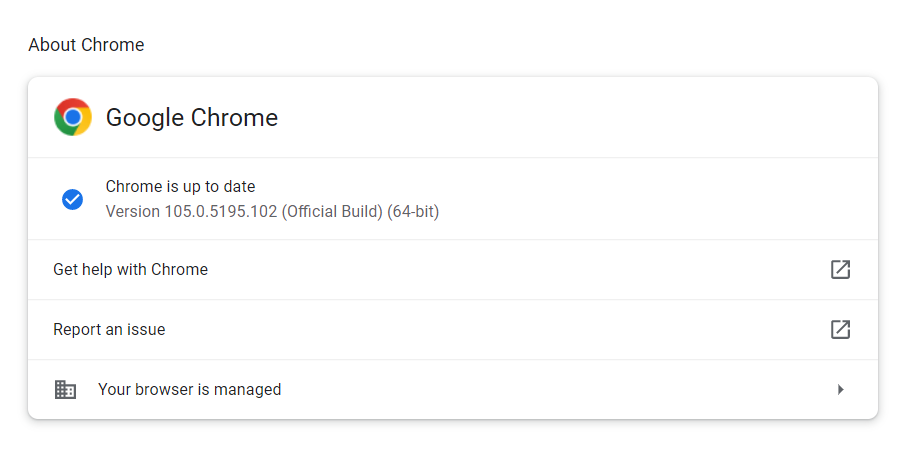
All the Google Chrome versions older than 105.0.5195.102 are affected by this vulnerability.
Mitigation
Customers are advised to upgrade to the latest Chrome version 105.0.5195.102. For more information, please refer to the Google Chrome security page.
The customer can check for the updates by navigating to Chrome menu > Help > About Google Chrome. The web browser will automatically check for the latest updates and install them when it is launched.
Microsoft has released the Microsoft Edge Stable Channel (version 105.0.1343.27) addressing the latest security updates of the Chromium project. This update contains a fix for CVE-2022-3075 reported by the Chromium team as having an exploit in the wild.
Qualys Detection
Qualys customers can scan their devices with QIDs 376965 and 376966 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2022-3075
https://chromereleases.googleblog.com/2022/09/stable-channel-update-for-desktop.html
https://www.bleepingcomputer.com/news/security/google-chrome-emergency-update-fixes-new-zero-day-used-in-attacks/