Welcome to another insightful dive into Microsoft’s Patch Tuesday! This month’s security updates address a vast number of vulnerabilities in multiple popular products, features, and roles. We invite you to join us to review and discuss the details of these security updates and patches.
Microsoft Patch Tuesday’s April 2024 edition addressed 155 vulnerabilities, including three critical and 145 important severity vulnerabilities. In this month’s security updates, Microsoft has not addressed any zero-day vulnerabilities known to be exploited in the wild. Microsoft also addressed three vulnerabilities in Microsoft Edge (Chromium-based). The vulnerabilities have been patched earlier this month.
Microsoft Patch Tuesday, April edition includes updates for vulnerabilities in Microsoft Office and Components, Microsoft Defender for IoT, Windows DHCP Server, DNS Server, Windows Hyper-V, SQL Server, Windows File Server Resource Management Service, Windows Proxy Driver, .NET and Visual Studio, Azure Compute Gallery, and more.
Microsoft has fixed several flaws in multiple software, including Denial of Service (DoS), Elevation of Privilege (EoP), Information Disclosure, Remote Code Execution (RCE), Security Feature Bypass, and Spoofing.
The April 2024 Microsoft vulnerabilities are classified as follows:
| Vulnerability Category | Quantity | Severities |
| Spoofing Vulnerability | 5 | Important: 5 |
| Denial of Service Vulnerability | 7 | Important: 7 |
| Elevation of Privilege Vulnerability | 31 | Important: 31 |
| Information Disclosure Vulnerability | 13 | Important: 12 |
| Remote Code Execution Vulnerability | 67 | Critical: 3 Important: 64 |
| Security Feature Bypass Vulnerability | 29 | Important: 28 |
Critical Severity Vulnerabilities Patched in April Patch Tuesday Edition
CVE-2024-21322: Microsoft Defender for IoT Remote Code Execution Vulnerability
Microsoft Defender for IoT is a tool that provides visibility and security across a network by identifying specialized protocols, devices, and machine-to-machine (M2M) behaviors. The tool protects enterprise IoT networks and supports cloud, on-premises, and hybrid OT networks.
An attacker must be an administrator of the web application to exploit the vulnerability. Successful exploitation of the vulnerability may lead to remote code execution on target systems.
CVE-2024-21323: Microsoft Defender for IoT Remote Code Execution Vulnerability
To exploit this path traversal vulnerability, an attacker must send a tar file to the Defender for the IoT sensor. After the extraction process, the attacker may send unsigned update packages and overwrite any file they choose. The attacker must first authenticate themselves and gain the necessary permissions to initiate the update process.
CVE-2024-29053: Microsoft Defender for IoT Remote Code Execution Vulnerability
An attacker must be authenticated to exploit the vulnerability, but no admin or other elevated privileges are required. Successful exploitation of this path traversal vulnerability requires an authenticated attacker, with access to the file upload feature, to upload malicious files to sensitive locations on the server.
Other Microsoft Vulnerability Highlights
- CVE-2024-26256 is a remote code execution vulnerability in libarchive. An attacker requires no authentication to exploit the vulnerability. An unauthorized attacker must wait for a user to initiate a connection for successful exploitation.
- CVE-2024-26158 is an elevation of privilege vulnerability in the Microsoft Install Service. On successful exploitation, an attacker could gain SYSTEM privileges.
- CVE-2024-26209 is an information disclosure vulnerability in Microsoft Local Security Authority Subsystem Service. On successful exploitation, an attacker may disclose uninitialized memory.
- CVE-2024-26218 is an elevation of privilege vulnerability in Windows Kernel. On successful exploitation, an attacker could gain SYSTEM privileges.
- CVE-2024-26234 is a spoofing vulnerability in Proxy Driver. Microsoft has not disclosed any information about the vulnerability.
- CVE-2024-26211 is an elevation of privilege vulnerability in Windows Remote Access Connection Manager. On successful exploitation, an attacker could gain SYSTEM privileges.
- CVE-2024-26212 is a denial-of-service vulnerability in the DHCP Server Service. Microsoft has not disclosed any information about the vulnerability.
- CVE-2024-26230 and CVE-2024-26239 are elevation of privilege vulnerabilities in the Windows Telephony Server. On successful exploitation, an attacker could gain SYSTEM privileges.
- CVE-2024-29056 is an elevation of privilege vulnerability in Windows Authentication. An attacker who successfully exploits the vulnerability may view some sensitive information. The advisory states, “The updates released on or after April 9, 2024, will NOT fully address the security issues in this vulnerability. For more information about how to manage PAC validation changes related to this CVE and the steps you need to take to be fully protected, see How to manage PAC Validation changes related to CVE-2024-26248 and CVE-2024-29056.”
- CVE-2024-29988 is a security feature bypass vulnerability in SmartScreen Prompt. To exploit this vulnerability, an attacker must convince a user to launch malicious files using a launcher application that requests that no UI be shown.
- CVE-2024-26241 is an elevation of privilege vulnerability in Win32k. On successful exploitation, an attacker could gain SYSTEM privileges.
- CVE-2024-28921 & CVE-2024-28903 are security feature bypass vulnerabilities in Secure Boot. Successful exploitation of the vulnerability may allow an attacker to bypass Secure Boot. Microsoft mentioned in the advisory, “All customers should apply the April 9, 2024, Windows security updates. These security updates address this vulnerability by updating the Windows Boot Manager and other components, but the protections are not enabled by default. Additional steps are required to mitigate this vulnerability. Please refer to KB5025885.”
Microsoft Release Summary
This month’s release notes cover multiple Microsoft product families and products/versions affected, including, but not limited to, Windows BitLocker, Windows Secure Boot, Microsoft Office Outlook, Windows Remote Procedure Call, Azure Private 5G Core, Windows Kernel, Windows Authentication Methods, Microsoft Install Service, Windows DWM Core Library, Windows Routing and Remote Access Service (RRAS), Windows Kerberos, Azure Migrate, Windows Remote Access Connection Manager, Windows Message Queuing, Windows Local Security Authority Subsystem Service (LSASS), Microsoft WDAC OLE DB provider for SQL, Microsoft Brokering File System, Microsoft WDAC ODBC Driver, Windows HTTP.sys, Windows Mobile Hotspot, Windows Distributed File System (DFS), Windows Cryptographic Services, Windows Update Stack, Windows Defender Credential Guard, Windows Win32K – ICOMP, Windows Telephony Server, Windows USB Print Driver, Microsoft Office SharePoint, Windows Internet Connection Sharing (ICS), Windows Virtual Machine Bus, Windows Compressed Folder, Microsoft Office Excel, Azure Arc, Microsoft Edge (Chromium-based), Windows, Azure AI Search, Internet Shortcut Files, Azure Monitor, Microsoft Azure Kubernetes Service, Azure SDK, Azure, and Intel.
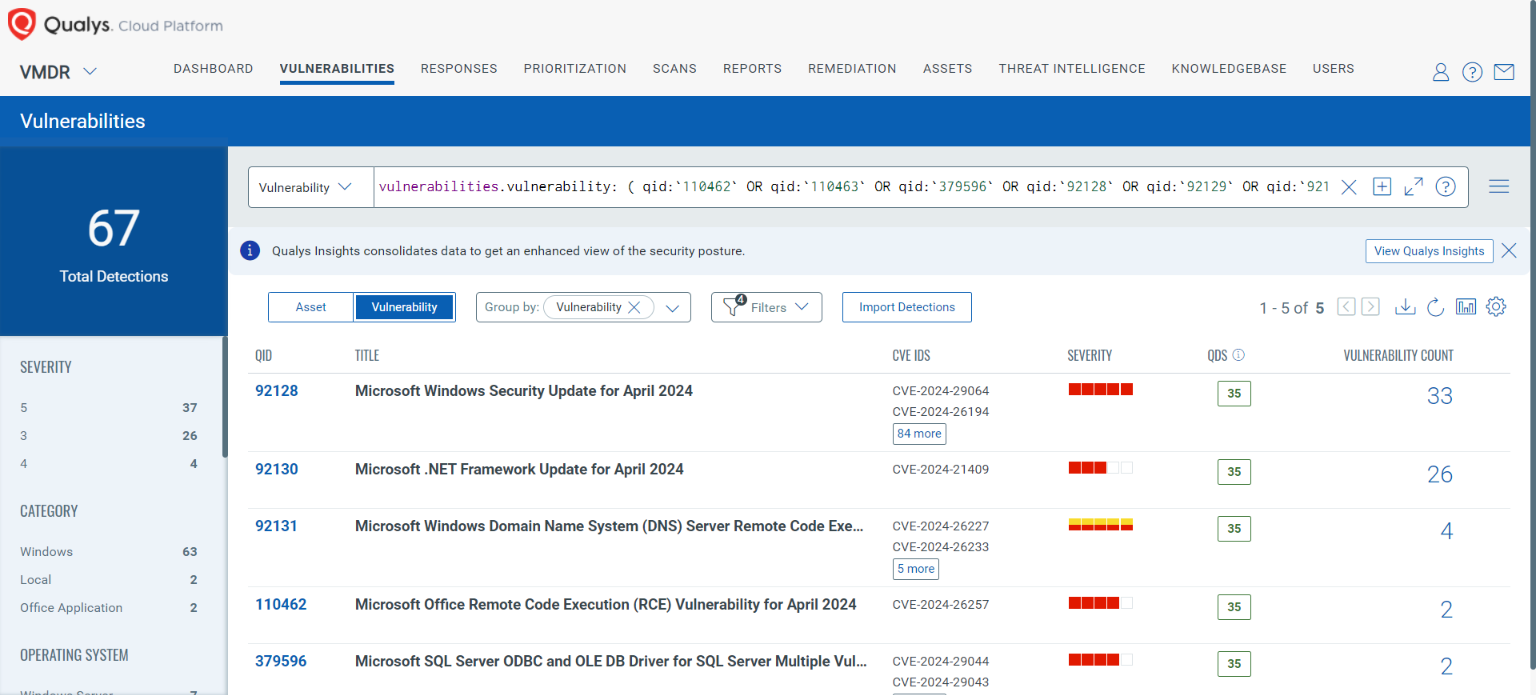
Discover and Prioritize Vulnerabilities in Vulnerability Management, Detection & Response (VMDR)
Qualys VMDR automatically detects new Patch Tuesday vulnerabilities using continuous updates to its Knowledgebase (KB).
You can see all your impacted hosts by these vulnerabilities using the following QQL query:
vulnerabilities.vulnerability: ( qid:`110462` OR qid:`110463` OR qid:`379596` OR qid:`92128` OR qid:`92129` OR qid:`92130` OR qid:`92131` OR qid:`92132` OR qid:`92133` )
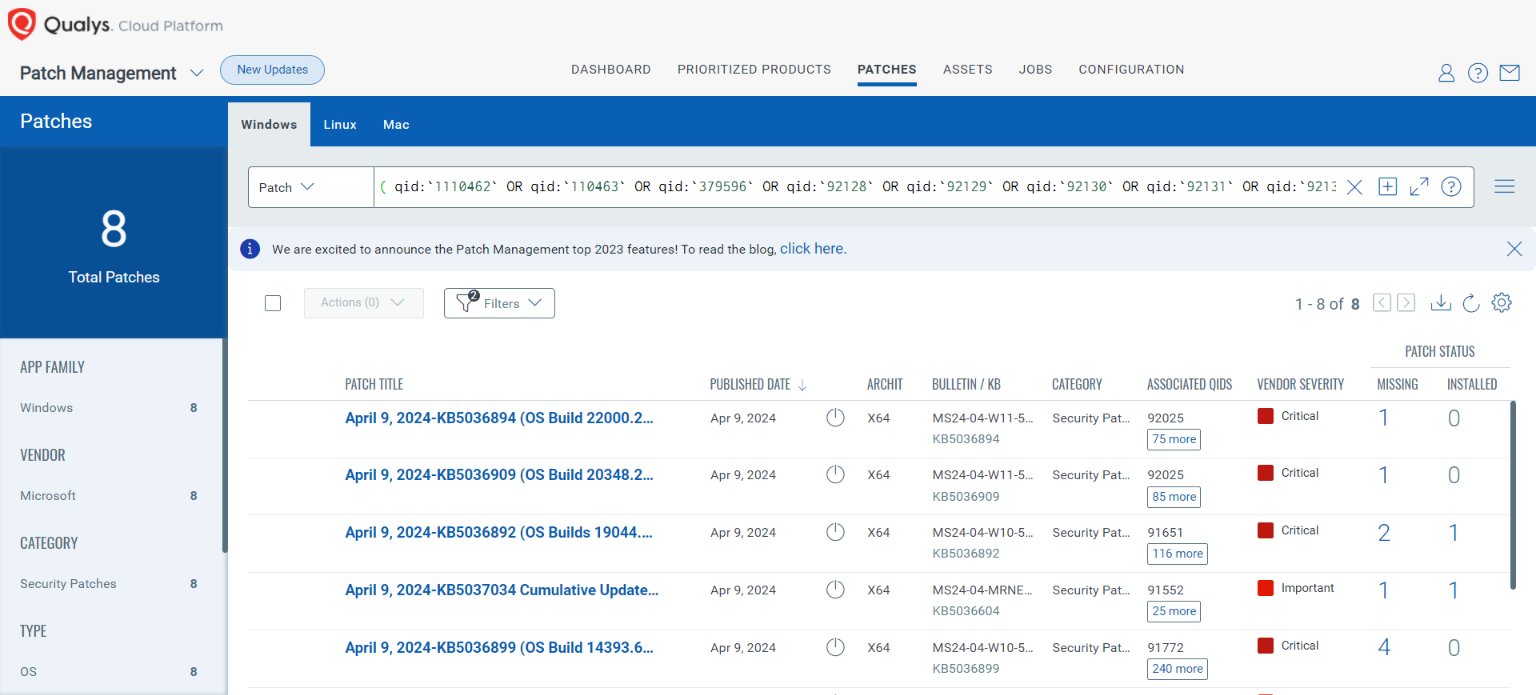
Rapid Response with Patch Management (PM)
VMDR rapidly remediates Windows hosts by deploying the most relevant and applicable per-technology version patches. You can simply select respective QIDs in the Patch Catalog and filter on the “Missing” patches to identify and deploy the applicable, available patches with one click.
The following QQL will return the missing patches for this Patch Tuesday:
( qid:`1110462` OR qid:`110463` OR qid:`379596` OR qid:`92128` OR qid:`92129` OR qid:`92130` OR qid:`92131` OR qid:`92132` OR qid:`92133` )
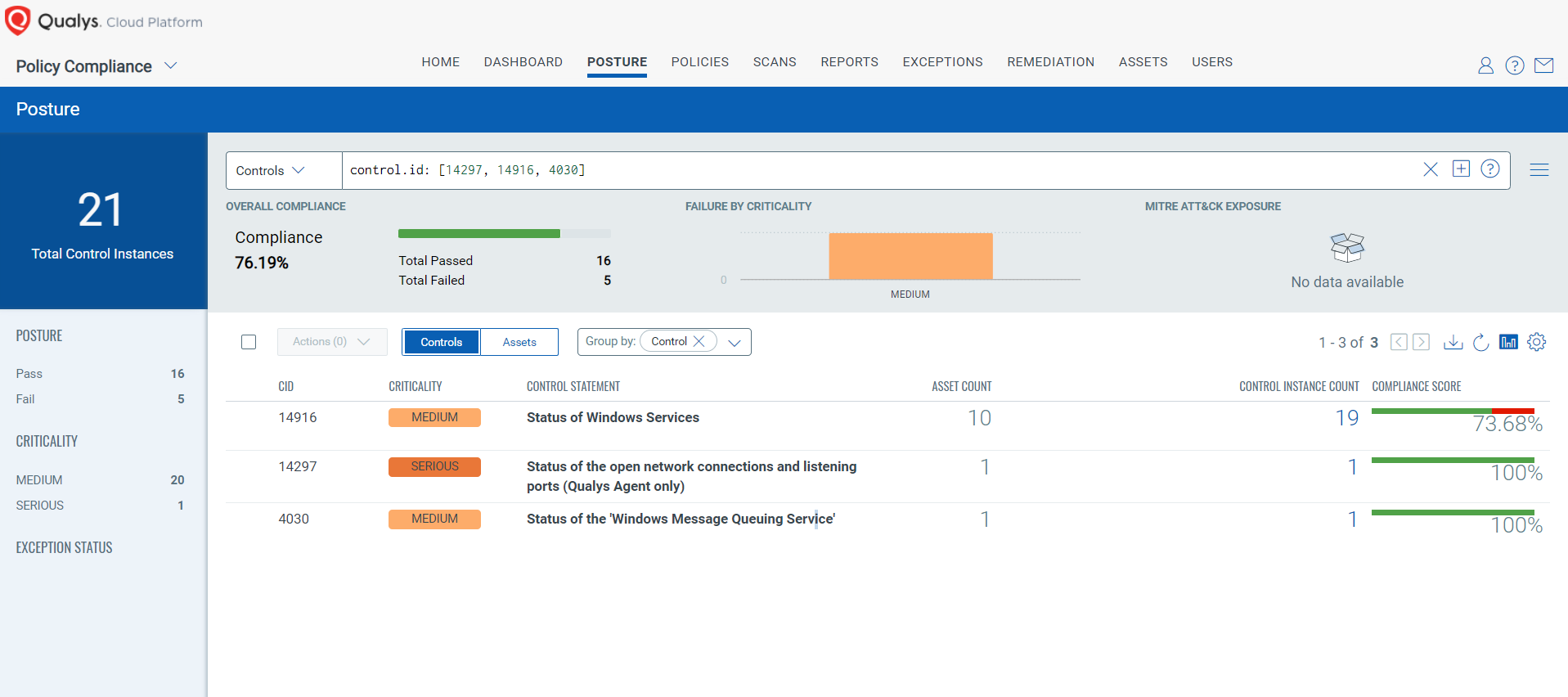
EVALUATE Vendor-Suggested Mitigation with Policy Compliance (PC)
With Qualys Policy Compliance’s Out-of-the-Box Mitigation or Compensatory Controls, the risk of a vulnerability being exploited is reduced when the remediation (fix/patch) cannot be implemented immediately.
Qualys Policy Compliance team releases these exclusive controls based on vendor-suggested Mitigation/Workaround.
Mitigation refers to a setting, standard configuration, or general best-practice existing in a default state that could reduce the severity of the exploitation of a vulnerability.
A workaround is sometimes used temporarily to achieve a task or goal when the usual or planned method isn’t working. Information technology often uses a workaround to overcome hardware, programming, or communication problems. Once a problem is fixed, a workaround is usually abandoned.
The following Qualys Policy Compliance Control IDs (CIDs), and System Defined Controls (SDC) have been updated to support Microsoft recommended mitigation(s) for this Patch Tuesday:
CVE-2024-26232: Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability
CVSS:3.1 7.3 / 6.4
Policy Compliance Control IDs (CIDs):
- 14297 Status of the open network connections and listening ports (Qualys Agent only)
- 14916 Status of Windows Services
- 4030 Status of the Windows Message Queuing Service
The following QQL will return a posture assessment for the CIDs for this Patch Tuesday:
control.id: [14297, 14916, 4030]
Visit the April 2024 Security Updates page to access the full description of each vulnerability and the systems it affects.
Qualys customers can scan their network with QIDs 110462, 110463, 379596, 92128, 92129, 92130, 92131, 92132, and 92133 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References:
https://msrc.microsoft.com/update-guide/
https://msrc.microsoft.com/update-guide/releaseNote/2024-Apr
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-29053
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-21322
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-21323