Chrome has released security updates for Windows, Mac, and Linux to fix the zero-day vulnerability. Tracked as CVE-2022-4262, it is a type confusion vulnerability in the V8 JavaScript engine. Clement Lecigne of Google’s Threat Analysis Group has reported this vulnerability.
Google has acknowledged the active exploitation of this vulnerability in the wild.
A type confusion flaw occurs when a code section uses an object without inspecting the type of object supplied to it. As a type is specified as a memory layout in the lower-level implementation of Flash Player, type confusion can be extremely dangerous. Wrong function pointers or data can also be sent to the wrong piece of code due to type confusion which can result in code execution.
CVE-2022-4262 is the ninth zero-day vulnerability in the Chrome browser that Google has fixed since the start of the year. The previous zero days were:
- CVE-2022-4135: Heap buffer overflow vulnerability in GPU (November 24th)
- CVE-2022-3723: Type Confusion in V8 (October 27th)
- CVE-2022-3075: Insufficient data validation in Mojo (September 2nd)
- CVE-2022-2856: Insufficient validation of untrusted input in Intents (August 17th)
- CVE-2022-2294: Heap-based buffer overflow vulnerability in the WebRTC (Web Real-Time Communications) component (July 4th)
- CVE-2022-1364: Type confusion in V8 (April 14th)
- CVE-2022-1096: Type confusion flaw in the Chrome V8 JavaScript engine (March 25th)
- CVE-2022-0609: Use-after-free in Animation (February 14th)
CISA has added this vulnerability to its Known Exploited Vulnerabilities Catalog and asked the security teams to patch the vulnerability by Dec 26th.
Affected versions
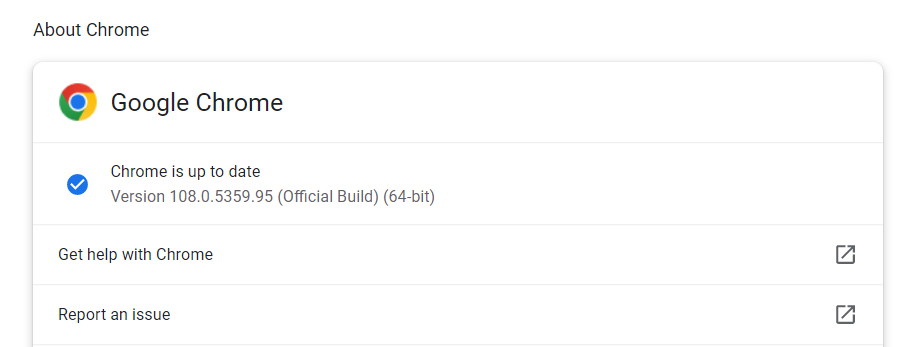
Google Chrome versions prior to 108.0.5359.94 are affected by this vulnerability.
Mitigation
Customers are requested to upgrade to the latest stable channel version, 108.0.5359.94 for Mac and Linux and 108.0.5359.94/.95 for Windows. For more information, please refer to the Google Chrome security page.
The customer can check for the updates by navigating to Chrome Menu > Help > About Google Chrome. The web browser automatically checks for the latest updates and installs them when launched.
Microsoft has released the Microsoft Edge Stable Channel (Version 108.0.1462.41). With a fix for CVE-2022-4262, which the Chromium team has reported as having an exploit in the wild.
Qualys Detection
Qualys customers can scan their devices with QIDs 377804 and 377805 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References
https://chromereleases.googleblog.com/2022/12/stable-channel-update-for-desktop.html
https://learn.microsoft.com/en-us/deployedge/microsoft-edge-relnotes-security#december-5-2022